SPOTLIGHT
Your Plan Of Action to Ensure File Transfer Security – Coviant Software
DOWNLOAD NOW
 Click here to download this whitepaper.
Click here to download this whitepaper.
 Click here to download this whitepaper.
Click here to download this whitepaper.

Click here to download this whitepaper.
Click here to download this whitepaper.
Click here to download the whitepaper
International Regulatory Compliance Whitepaper
Free Whitepaper: The key changes in the ISO/IEC 27002:2022
by SGS
Are you implementing ISO/IEC 27001 to govern your Information Security Management System? If so, did you know that the controls in the guidance document, ISO/IEC 27002, have recently changed, directly impacting the controls in ISO/IEC 27001’s Annex A? While the latest controls will be phased in with the new version of ISO/IEC 27001 due to be released later this year, make sure to get ahead by reviewing the changes early in SGS’ newest white paper.
Click here to download a free copy of this whitepaper.
Managed File Transfer Software Solutions & MFT Tools
Click here to download the case study
IT & Legal: Why CISOs Must Partner with Legal to Effectively Protect Your Business
 Each year, the Association of Corporate Counsel (ACC) releases their much-anticipated Chief Legal Officers Survey, which represents one of the most comprehensive collections of insights from general counsel and CLOs across a wide range of companies and industries. For more than 20 years, the ACC’s flagship study has provided crucial, high-quality data on the state of the corporate legal department and the evolving role of the CLO. This year, Exterro, the ACC’s Alliance Partner for E-Discovery, Data Privacy and Cybersecurity Compliance, was thrilled to sponsor the survey. In looking at the data from another lens—through the eyes of the Chief Information Officer/Chief Information Security Officer (CIO/CISO)—we’ve identified some areas in which there is clear alignment between CISOs and CLOs, as well as some areas of divergence. Some of those disagreements represent significant challenges in successful implementation of an enterprise Legal Governance, Risk and Compliance (GRC) strategy, which we’ll take a closer look at below. In this whitepaper, we’ll examine how IT departments can work more effectively with Legal to handle and prepare for growing data challenges/requirements.
Each year, the Association of Corporate Counsel (ACC) releases their much-anticipated Chief Legal Officers Survey, which represents one of the most comprehensive collections of insights from general counsel and CLOs across a wide range of companies and industries. For more than 20 years, the ACC’s flagship study has provided crucial, high-quality data on the state of the corporate legal department and the evolving role of the CLO. This year, Exterro, the ACC’s Alliance Partner for E-Discovery, Data Privacy and Cybersecurity Compliance, was thrilled to sponsor the survey. In looking at the data from another lens—through the eyes of the Chief Information Officer/Chief Information Security Officer (CIO/CISO)—we’ve identified some areas in which there is clear alignment between CISOs and CLOs, as well as some areas of divergence. Some of those disagreements represent significant challenges in successful implementation of an enterprise Legal Governance, Risk and Compliance (GRC) strategy, which we’ll take a closer look at below. In this whitepaper, we’ll examine how IT departments can work more effectively with Legal to handle and prepare for growing data challenges/requirements.
Click here to download a free copy of this whitepaper.
Whitepaper Library
AI Driven Threat Defense: The Next Frontier in Cyber Security | IT & Legal: Why CISOs must partner with Legal to protect your business. | A new approach to help you achieve least privilege at cloud scale |
The Guide to Passwordless Anywhere: Implementing a unified credential management platform. | Active Directory is Now The Number One Target of Hackers – Learn How to Harden It – Today! | How To Prevent Your ERP Security And Compliance Requirements From Slowing Down Your Digital Transformation |
Cyber Defense for Semiconductor | RiskSense: Q1 2021 Ransomware Index Update: Through the Lens of Threat and Vulnerability Management. | IDC Provides a Solution Checklist for Transforming Zero Trust Principles to Reliable Practices |
How Cryptoloc Can Solve your GDPR Data Transfer Issues | A New Approach to Malware Analysis | Sangfor XDDR: Security Synergy |
Executive Protection at Home is the Major Gap in Cybersecurity | What is Attack Surface Management? | Why Microsoft Is Now the Leader in Endpoint Detection |
Winds of change: causes and implications of the SolarWinds compromise | Packet Capture is a Foundational Technology | Choosing a cyber security solution. Your guide to getting it right. |
Active Directory is Now The Number One Target of Hackers – Learn How to Harden It – Today! | Analysis of security vulnerabilities in WordPress ecosystem | IDC Provides a Solution Checklist for Transforming Zero Trust Principles to Reliable Practices |
IT & Legal: Why CISOs Must Partner with Legal to Effectively Protect Your Business
 Each year, the Association of Corporate Counsel (ACC) releases their much-anticipated Chief Legal Officers Survey, which represents one of the most comprehensive collections of insights from general counsel and CLOs across a wide range of companies and industries. For more than 20 years, the ACC’s flagship study has provided crucial, high-quality data on the state of the corporate legal department and the evolving role of the CLO. This year, Exterro, the ACC’s Alliance Partner for E-Discovery, Data Privacy and Cybersecurity Compliance, was thrilled to sponsor the survey. In looking at the data from another lens—through the eyes of the Chief Information Officer/Chief Information Security Officer (CIO/CISO)—we’ve identified some areas in which there is clear alignment between CISOs and CLOs, as well as some areas of divergence. Some of those disagreements represent significant challenges in successful implementation of an enterprise Legal Governance, Risk and Compliance (GRC) strategy, which we’ll take a closer look at below. In this whitepaper, we’ll examine how IT departments can work more effectively with Legal to handle and prepare for growing data challenges/requirements.
Each year, the Association of Corporate Counsel (ACC) releases their much-anticipated Chief Legal Officers Survey, which represents one of the most comprehensive collections of insights from general counsel and CLOs across a wide range of companies and industries. For more than 20 years, the ACC’s flagship study has provided crucial, high-quality data on the state of the corporate legal department and the evolving role of the CLO. This year, Exterro, the ACC’s Alliance Partner for E-Discovery, Data Privacy and Cybersecurity Compliance, was thrilled to sponsor the survey. In looking at the data from another lens—through the eyes of the Chief Information Officer/Chief Information Security Officer (CIO/CISO)—we’ve identified some areas in which there is clear alignment between CISOs and CLOs, as well as some areas of divergence. Some of those disagreements represent significant challenges in successful implementation of an enterprise Legal Governance, Risk and Compliance (GRC) strategy, which we’ll take a closer look at below. In this whitepaper, we’ll examine how IT departments can work more effectively with Legal to handle and prepare for growing data challenges/requirements.
Click here to download a free copy of this whitepaper.
AI Driven Threat Defense: The Next Frontier in Cyber Security
Anyone who follows the state of cybersecurity understands that cyber attacks have increased, becoming ever more targeted, elusive, and damaging. Emerging technologies, like the Internet of Things, artificial intelligence, and hybrid cloud computing, are expanding the attack surface, making detection and understanding the full scope of today’s attacks much more challenging. Today, the enterprise security strategy needs to shift from pre-breach prevention to fast, post-breach detection and mitigation.
Click here to download a free copy.
A new approach to help you achieve least privilege at cloud scale
One bad human identity. One poorly configured firewall. One machine identity with excessive high-risk permissions. Three commands.
That’s all it took to expose the personal data of millions of customers of a major US-based bank in a widely reported 2019 security breach. The breach, which led to fines of over $80 million to the institution, resulted from a hacker that took advantage of an over-permissioned AWS role, which in this case included the ability to discover and exfiltrate personal identifying information.
The proper Cloud Infrastructure Entitlement Management (CIEM) platform can prevent your organization from experiencing a similar breach.
What CIEM Solves
- Lack of visibility into permissions granted and used (Permissions Gap)
- Enforce least privilege policies across all identities
- Provide Privileged Access on-demand
Benefits
- Comprehensive visibility into identity and resource Permissions Gap
- Cross-Account Access visualization
- Automatically Remediate over-permissioned identities (user, role, group, resource) to create least privileged roles/policies
- Deliver Permissions-on-Demand & Just-in-Time Permissions which are time and resource bound
Click here to download a free copy of our whitepaper.
How To Prevent Your ERP Security And Compliance Requirements From Slowing Down Your Digital Transformation
Digital Transformation And ERP Modernization Are Two Sides Of The Same Coin.
As your organization tackles its digital transformation journey, cloud-based ERP is often seen as a solution to many of these problems. However, modernizing legacy ERP systems like SAP ECC, Oracle PeopleSoft, and Oracle EBS creates a quandary: How do you maximize the access and availability of your ERP without sacrificing the security and integrity of your business-critical data during a digital transformation?
In this white paper, we discuss how organizations with legacy ERP systems must determine the right mix between digital transformation and modernization so they’re not “sacrificing” data security, privacy, or compliance policies. Taking a proactive, data-centric approach to ERP security and data privacy during your company’s digital transformation can mitigate risks before they turn into realities.
Click here to download a free copy.
The Guide to Passwordless Anywhere
As remote work increases and our digital environments change, going passwordless is essential for the security of all enterprises. With remote teams, cloud applications, and multiple devices, it can be difficult to protect your private information. By implementing a unified credential management platform you can secure all the users and machines on your network without compromising on cost or usability.
In this guide, you will learn:
-
Why passwordless authentication is essential to securing your digital identities
-
The best practices to make authentication user-centric and secure
-
How to simplify the journey to passwordless with a single identity platform solution
Click here to download a free copy.
RiskSense: Q1 2021 Ransomware Index Update
Ransomware Index Update will help organizations gain an insight into what vulnerabilities could render them susceptible to ransomware continuing the research from our Ransomware 2021, Through the Lens of Threat and Vulnerability Management.
Click here to download a free copy.
Cyber Defense for Semiconductor Foundries: Safeguarding Digital Innovation
A cyber attack on a semiconductor fab can cause tens of millions of dollars in damages to the stakeholding organization in less than a day.
The damages of disruption by malware or Advanced Persistent Threat (APT) groups are difficult to overstate: far-reaching effects ripple out, afflicting every downstream link in the supply chain and in essence forcing global progress to run backwards. The introduction of a new set of comprehensive standards, as well as the gear for maintaining these standards, will be what provides wafer fabs with the security necessary to create the technologies of the future.
Click here to download a free copy.
The Cybersecurity Cocktail Book
SCADABAR
Raise Your Drinks & Your OT/ IoT Security Posture
In today’s stressful times, we can all use a refreshing beverage.
Seriously, with the uncertainty around the ongoing attacks on industrial controls systems and with rising ransomware incidents, we can all use some brightness in our lives.
The SCADAfence team have put this cocktail book together for you. We hope it will help you enjoy your week a little better.
Click here to download a free copy.
How Cryptoloc Can Solve your GDPR Data Transfer Issues
Cryptoloc as a Supplementary Measure to protect Personal Data Transfers
The introduction of the General Data Protection Regulation (GDPR) and associated stiffer penalties and increased enforcement activity has highlighted the global importance of ensuring data protection, particularly for entities dealing with personal data on an international basis.
This whitepaper considers the following:
- What are the essential requirements for encryption to be a suitable supplementary measure for transferring data out of the
EEA; and - How the Cryptoloc solution meets those requirements
Click here to download a free copy.
A new approach to malware analysis
Malware is a constant threat to organizations around the world. Open an email and you may lose a lot of money, data, and reputation. Different tools can help to overcome these situations.
After the attack cybersecurity analytics usually collect and investigate a malicious program to find out its type and functions. The best way to do this safely is by sandboxing.
Today, most malware samples are polymorphic. This means that they are equipped with a mutation engine that can change certain parameters like file names and hash sums, completely throwing off antiviruses. Emotet Trojan and Qbot are examples of widely known malware families that use
polymorphism.
One way to overcome the challenge is to use sandboxes.
Click here to download a free copy.
Sangfor XDDR: Security Synergy
Syngery = eXtended Detection, Defense & Response
While Enhanced Detection & Response (XDR) products have become very popular, they have not done well defending
systems from malware and APT threats. Their biggest limitation is, being endpoint protection, they do not truly coordinate
with network devices; no sharing of anomalous behavior or coordinating responses.
Sangfor XDDR is a framework that goes beyond traditional XDR by implementing a real integrated security solution,
providing holistic response to malware infections and APT breaches across the entire organization’s network, with ease
of management, operation, and maintenance
Click here to download a free copy.
Executive Protection at Home is the Major Gap in Cybersecurity
An Educational White Paper
Learn more about the state of personal cybersecurity & privacy for executives and key personnel, how it affects their companies, and what you can do about it.
Protect Your Company by Protecting Your ExecutivesTM
Easier targets with high-authority level naturally are targeted more often. For example, according to the recent Verizon DBIR:
- C-suite executives were 12 times more likely to be targeted in cyber attacks
- 71 percent of C-suite cyberattacks were financially motivated
Click here to download a free copy.
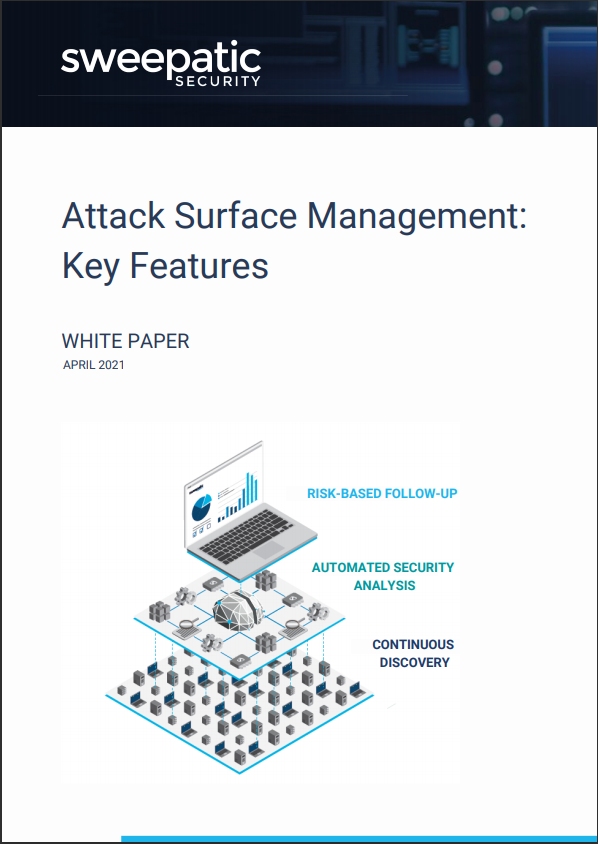
What is Attack Surface Management?
Attack Surface Management: Key Features
A relatively new cyber security problem space with its own definition has been coined since a few years now: Attack Surface Management or ASM. The term can be confusing or vague without spending some time on a clear definition. In cybersecurity there are many ‘surfaces’ that can be attacked. So what surface are we talking about? In cybersecurity, the word ‘attack surface’ is interpreted as the publicly exposed or internet exposed or external exposed IT assets.
Click here for an instant download of this excellent resource.
Why Microsoft Is Now the Leader in Endpoint Detection
The cybersecurity industry is no stranger to assumptions. It’s the reason why the same established technology providers have been the focus for over a decade. It’s also the reason why Microsoft was historically overlooked as a reliable solution provider in this space.
But that’s all changing now.
Microsoft is serious about security, having invested over $1 billion USD in security development. This has pushed Microsoft to the leading edge of security across many technology areas.
Today, endpoint protection is one of the most obvious areas of improvement. The decades of Windows vulnerabilities and generic antivirus solutions that earned Microsoft its mediocre reputation are over.
For security-focused companies and industries, Microsoft shouldn’t be an afterthought—it should be the first choice.
Click here to download a free copy.
Winds of change: causes and implications of the SolarWinds compromise
Why is it important to understand the systemic factors driving this sophisticated attack?
SolarWinds did not come out of the blue and should not be regarded as such. It’s the inevitable consequence of a powerful set of systemic factors that collectively produce a climate that is inherently volatile but can still be predicted. While forecasts for a specific day may fail, the general tendency is driven by known forces and systems.
This volatile context currently strongly favours the attacker over the defender. That is not going to change unless the systemic drivers that create it are dealt with. In this case that means confronting and addressing some factors (like a massive investment by governments into computer hacking capabilities) and accepting and adapting to others (like the strong ties of interdependence that lie at the heart of cyberspace, the business ecosystem and indeed society in general).
Download your copy today.
“Visibility is the bedrock on which security teams operate and a strong packet capture solution provides the network visibility data to enable security teams to prevent, investigate, and remediate security incidents”
This whitepaper from leading cybersecurity analyst firm, TAG Cyber, outlines why always-on, full packet capture is such a critical component of an effective cybersecurity infrastructure and how it aligns with security frameworks such as NIST.
Click here to download a free copy.
 Choosing a cyber security solution.
Choosing a cyber security solution.
Your guide to getting it right.
Learn about:
-
-
-
-
-
- The benefits and limitations of
different technologies. - Assessing your cyber threat surface.
- Reducing attackable points in your IT infrastructure.
- What to look for in a modern
cyber security solution.
- The benefits and limitations of
-
-
-
-
Click here to download a free copy.
 Active Directory is Now The Number One Target of Hackers – Learn How to Harden It – Today!
Active Directory is Now The Number One Target of Hackers – Learn How to Harden It – Today!
Register for our Free eBook: The Secrets of Hardening Active Directory eBook
Click here to download a free copy.
Click here to download a free copy.
IDC Provides a Solution Checklist for Transforming Zero Trust Principles to Reliable Practices
Digital transformation (DX) is creating a highly fragmented, expanding, and dynamic footprint of applications, data, devices, end users, and networks. Implicit trust, unfortunately, is a casualty. Micro-segmentation can operationalize the principles of zero trust and least privilege in balancing risk and business activity.” IDC*
The attack surface that accompanies cloud adoption not only is expanding but also is brimming with change. IDC breaks down the common traits and security challenges that organizations share as they push forward their cloud journeys to boost speed and agility in IT operations.
KEY TAKEAWAYS
-
Zero trust and least privilege principles are critical as the risks of assumed trust are mounting.
-
Transforming principles to reliable practices is difficult.
-
Micro-segmentation eases the transformation of principles to reliable practices.
-
Micro-segmentation solutions vary.
Access the report now to read more about IDC’s solution checklist and recommendations for selecting an optimal micro-segmentation solution.
Click here to download a free copy.
More Whitepapers in Our Online Library: