Experts from security firm Wordfence discovered a Botnet of 20,000 WordPress Sites Infecting other WordPress installs.
Experts from security firm Wordfence uncovered a botnet composed of over 20,000 WordPress sites that is being used to compromise other websites running on the popular CMS and recruit them.
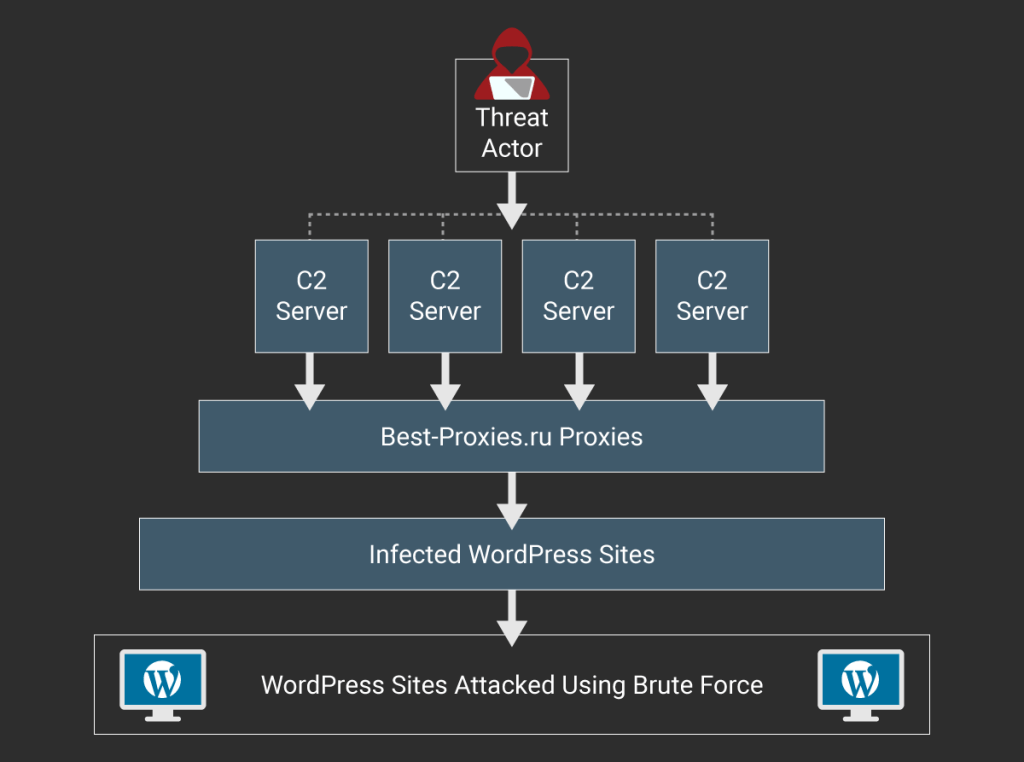
“The threat actors (hackers) use a group of four command and control (C2) servers to send requests to over 14,000 proxy servers provided by a Russian proxy provider called best-proxies[.]ru.” reads the analysis published by WordFence.
“They use these proxies to anonymize the C2 traffic. The requests pass through the proxy servers and are sent to over 20,000 infected WordPress sites. Those sites are running an attack script which attacks targeted WordPress sites.”
The botnet is used by attackers to carry out brute force attacks against other WordPress sites, according to Wordfence Defiant Threat Intelligence team, the botnet has already generated over 5 million authentication requests. The botnet attempts XML-RPC authentication to other WordPress sites in order to access privileged accounts.
The XML-RPC interface allows users to remotely post content to a WordPress site using the WordPress or other APIs, it is located in the root directory of a WordPress install at the xmlrpc.php file.
Unfortunately, the XML-RPC interface doesn’t implement a rate limiting on the number of API requests that it is possible to submit, a gift for brute-force attackers.
A close look at the malicious infrastructure allowed the experts to discover that hackers used four command and control servers that issue commands to the bots through proxy servers at the Russian Best-Proxies.ru service. Experts identified over 14,000 proxy servers used by the botmaster to anonymize the traffic.
Once a WordPress site is compromised it will start carrying out brute force attacks against the XML-RPC interface of other websites.
“We also noted that the User-Agent strings associated with these requests matched those used by applications commonly seen interacting with the XML-RPC interface, like wp-iphone and wp-android,” continues the analysis.
“Since these applications typically store credentials locally, it was unusual to see a significant amount of failed logins from them, which drew our attention. We identified over 20,000 WordPress slave sites that were attacking other WordPress sites.”
Brute force scripts used by the attackers accept POST input from the C2 servers, the request includes domains to target and word lists to use when performing the brute force attacks.
It is also possible to use new wordlists by providing URL to the script.
Wordfence reported its discovery to the authorities and is helping them to dismantle the WordPress botnet.