WannaCry made the headlines with the massive Ransomware attack that hit systems worldwide, what about an improved version?
WannaCry made the headlines with the massive Ransomware attack that hit systems worldwide.
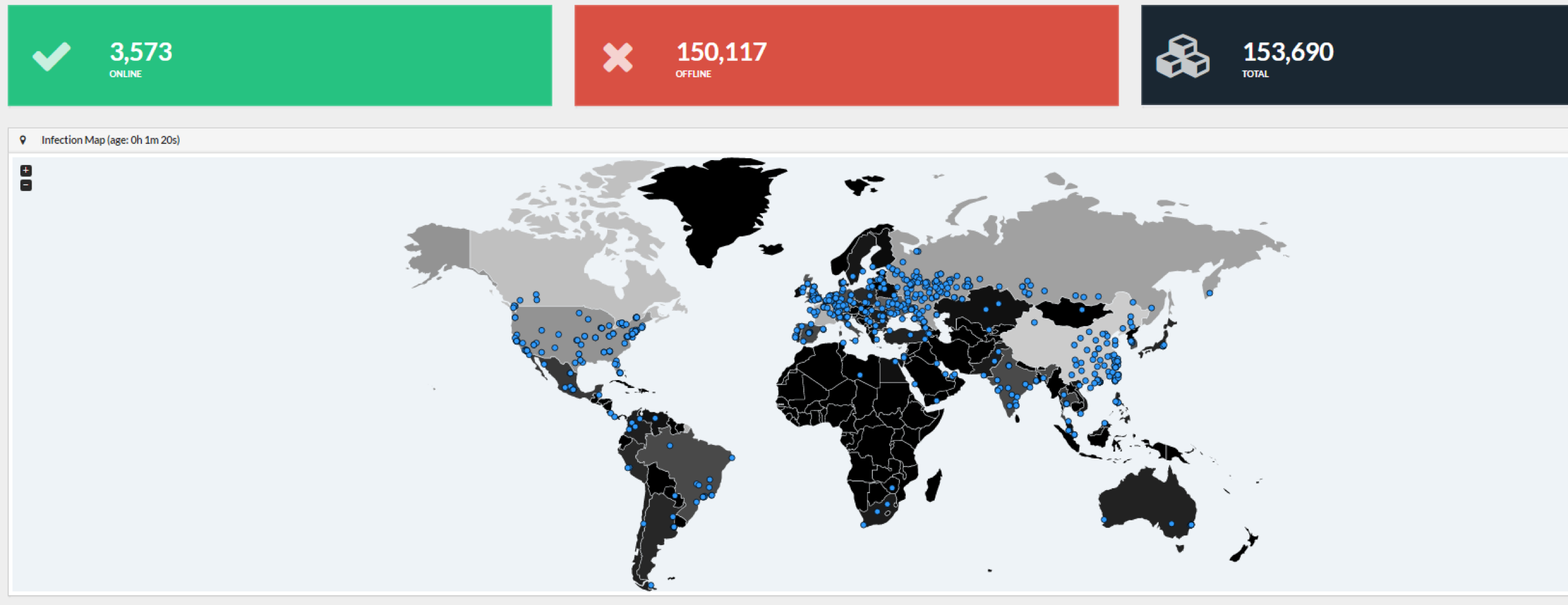
The malware targeted organizations across 99 countries worldwide, it leverages a Windows SMB exploit to compromise unpatched OS or computers running unsupported versions of Windows OS.
The WannaCry exploits the NSA EternalBlue / DoublePulsar exploits to infect other connected Windows systems on the same network, the malware implements network warm capabilities that allow it to rapidly spread.
“The special criticality of this campaign is caused by exploiting the vulnerability described in bulletin MS17-010 using EternalBlue / DoublePulsar, which can infect other connected Windows systems on the same network that are not properly updated. Infection of a single computer can end up compromising the entire corporate network.” states the security alert issued by the CERT.
“The ransomware, a variant of WannaCry, infects the machine by encrypting all its files and, using the vulnerability mentioned in the previous paragraph that allows the execution of remote commands through Samba (SMB) and is distributed to other Windows machines in That same network.”
The DOUBLEPULSAR backdoor allows attackers to inject and execute malicious code on a target system, it is installed by leveraging the ETERNALBLUE, an SMBv1 (Server Message Block 1.0) exploit that could trigger an RCE in older versions of Windows (Windows XP to Server 2008 R2).
While investigating the threat security researcher MalwareTech discovered the presence of a “Kill Switch” in the source code of the malware that once triggered will stop its diffusion.
The expert discovered that the malware check for the presence of a specific domain to start the infection process, then MalwareTech registered the domain sinkholing the malicious code.
At this point, something changed because the attacker took its countermeasure to disable the Kill Switch.
The security researcher and malware analyst, Luciano Martins is warning of the presence of a new variant of the dreaded ransomware that has no Kill-Switch in its code.
Martins explains that is too early to speak about a WannaCry 2.0 version, anyway the experts believe that threat actors in the wild could improve the threat.
If a variant without Kill Switch will be used in a new campaign it is quite simple to speculate a situation difficult to contain due to the huge number of unpatched systems.
“The next attacks are inevitable, you can simply patch the existing samples with a hex editor and it’ll continue to spread. We will see a number of variants of this attack over the coming weeks and months so it’s important to patch hosts.” Matthew Hickey, a security expert and co-founder of Hacker House told The Hacker News.
Hundreds of thousands of unpatched systems are still exposed on the Internet and vulnerable to the WannaCry ransomware attack. This last attack leveraged exclusively on SMB exploit but a possible future attack scenario sees the threat spreading via phishing or drive-by-download attacks.
“The worm can be modified to spread other payloads not just WCry and we may see other malware campaigns piggybacking off this samples success.” Hickey added.
Below an interesting demo of WannaCry Ransomware Infection shared by Matthew, the videos were first published by the friends at The Hacker News, but I believe it is essential to share them too.

In order to mitigate the threat, users have to Install Security Patches and Disable SMBv1 as suggested the experts.
Microsoft took an unusual step to protect its customers, the company released patches for Windows Server 2003 (SP2 x64 / x86); Windows XP (SP2 x64, SP3 x86); Windows XP Embedded (SP3, x86); as well as the 32-bit and 64-bit versions of Windows 8.
The Spanish CERT has released a script for temporarily (until reboot) mitigating the #WannaCry infection.