Security experts discovered last week that a US government website was hosting a JavaScript downloader used to deliver the Cerber ransomware.
The security researcher at NewSky Security Ankit Anubhav discovered last week that a US government website was hosting a malicious JavaScript downloader that was delivering the dreaded Cerber ransomware.
#Javascript #malware using #powershell hosted on US Government site. Link is still live! cc @USCERT_gov
IOC :: https://t.co/Thoyom3PTF pic.twitter.com/OjX9M7OzDU— Ankit Anubhav (@ankit_anubhav) August 30, 2017
“Javascript malware hosted on US government site which launches powershell to connect to C2.” said the researcher Ankit Anubhav from NewSky Security.
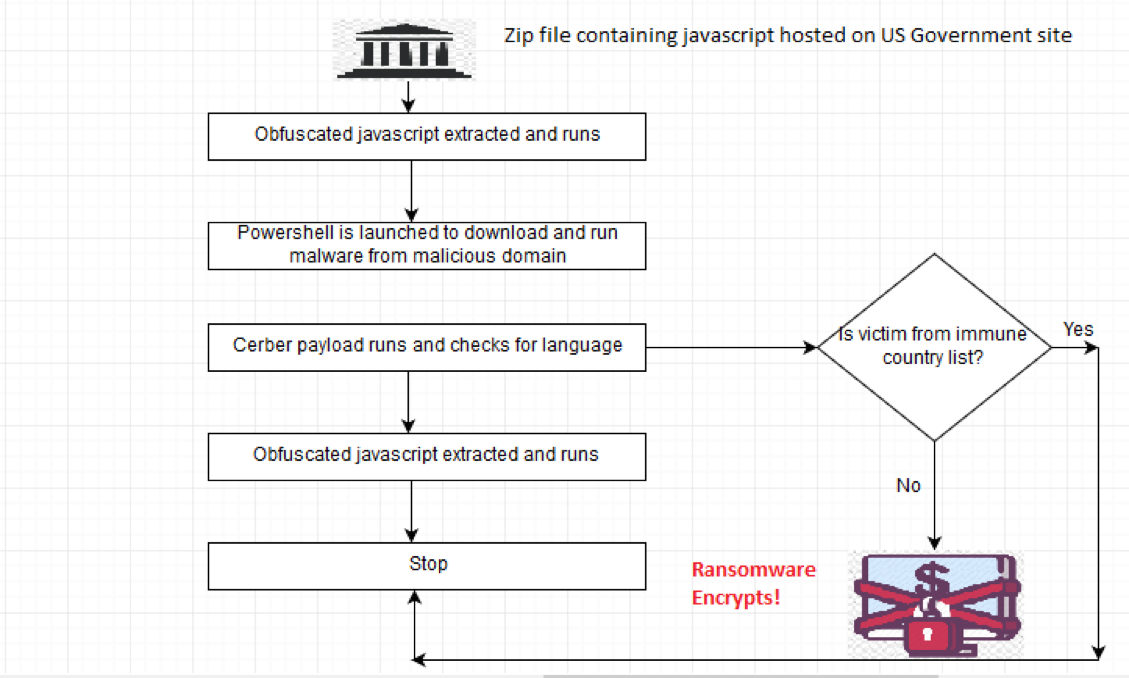
The website was hosting a .zip archive that contained JavaScript that included obfuscated PowerShell. The PowerShell downloads a gif file which is in reality a Cerber executable. Below the malicious link:
hxxp://dms(dot)nwcg(dot)gov/pipermail/ross-suggestion/attachments/20170304/9ee8a89e/attachment.zip
The downloader was spotted on Wednesday, and within hours, the malicious code was removed.
It is not clear how the attackers installed the malicious code onto the .gov site and how many visitors have been infected.
Anubhav believes that the site was compromised, another possibility is that the site was used as a storage for email attachments from government officials’ emails and probably the malware was attached to one of the messages.
The expert highlighted many similarities with the Blank Slate spam campaign which earlier this year was spreading the Cerber ransomware. The email used by crooks in this campaign contained a double-zip archive with the second containing either a malicious JavaScript file or a malicious Microsoft Word document.
“An interesting aspect of this campaign is that the file attachments are double-zipped. There’s a zip archive within the zip archive. Within that second zip archive, you’ll find a malicious JavaScript (.js) file or a Microsoft Word document. These files are designed to infect a computer with ransomware.” reported the analysis from SANS.
“Blank Slate has pushed different types of ransomware. However, the vast majority of ransomware from this campaign has been Cerber.”
According to an analysis published by Anubhav along with the malware analyst at Spanish telco Telefonica, Mariano Palomo Villafranca, high reputation websites like the US one hosting the malware represent a privileged attack vector for crooks.
“Often security solutions blacklist an entire range of IP addresses and the potential target is saved from such attack (because the site is blocked before they visit it). To counter this measure, attackers focus on hosting malware in legitimate places, such as Google documents, or websites which are “known/proven clean”. As it turns out, one ideal scenario for an attacker would be to host malware on a government site.” states the analysis published by the security duo.
In an attack scenario, a victim could receive a link to the page hosting the .zip file. Once the victim clicks on the link the obfuscated JavaScript is extracted and launches PowerShell which downloads the malware from a known a domain compromised by the attacker.
According to the analysis, the gif executable was a NSIS installer which was used to extract the Cerber JSON file configuration.
“The link is down as of now. However, when we analysed archived data, we found that this particular payload was Cerber ransomware with a SHA256 1f15415da53df8a8e0197aa7e17e594d24ea6d7fbe80fe3bb4a5cd41bc8f09f6.”
[adrotate banner=”9″]