Attackers have taken over the official domain name of The Perl Foundation perl.com and pointed it to an IP address associated with malware campaigns. Users are recommended to avoid visiting the domain.
The domain Perl.com was created in 1994 and was the official website for the Perl programming language, it is registered with the registrar key-systems(.)net.
“The perl.com domain was hijacked this morning and is currently pointing to a parking site. Work is ongoing to attempt to recover it.” reads the announcement published on the Perl NOC.
“We encourage you NOT to visit the domain, as there are some signals that it may be related to sites that have distributed malware in the past.”
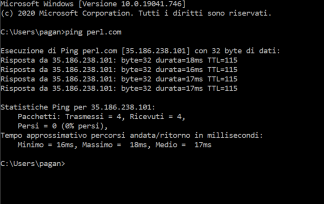
The attackers changed the IP address from 151.101.2.132 to 35.186.238[.]10.
After the hackers took over the site, it was displaying a blank page whose HTML contains Godaddy parked domain scripts.
Shortly after the domain hijacking, perl.com was offered for sale for $190k on afternic.com.
Users have to avoid using perl.com as CPAN mirror and can update their mirror in CPAN.pm use o conf urllist http://www.cpan.org/
# perl -MCPAN -eshell
cpan shell — CPAN exploration and modules installation (v2.20)
Enter ‘h’ for help.
cpan[1]> o conf urllist http://www.cpan.org/
Please use ‘o conf commit’ to make the config permanent!
cpan[2]> o conf commit
commit: wrote ‘/root/.cpan/CPAN/MyConfig.pm’
The 35.186.238[.]101 was associated with a domain employed in malware campaigns, including the distribution of Locky ransomware.
If you want to receive the weekly Security Affairs Newsletter for free subscribe here.
(SecurityAffairs – hacking, domain hijacking)


 Pierluigi Paganini
Pierluigi Paganini