.Security experts at Check Point discovered a new backdoor dubbed
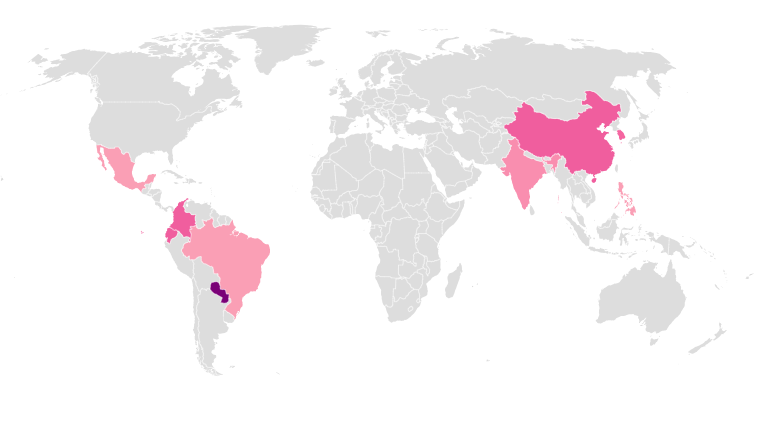
‘SpeakUp’ targeting Linux servers in East Asia and Latin America.
Malware researchers at Check Point have spotted a new Linux backdoor dubbed ‘SpeakUp’ targeting servers in East Asia and Latin America,
The SpeakUp backdoor leverages known vulnerabilities in six different Linux distros, it is also able to infect Mac systems. The Trojan spread by exploiting remote code execution flaw and for the initial infection hackers leverage recently disclosed flaw in ThinkPHP (CVE-2018-20062).
Researchers linked the author of the SpeakUp backdoor with the malware developer that goes online with the moniker of Zettabithf.
Most of the infected machines are in China, the same country where was spotted the sample analyzed by Check Point on January 14, 2019.
“The sample we analyzed was observed targeting a machine in China on January 14, 2019 and was first submitted to VirusTotal on January 9 2019. At the time of writing this article, it has no detections in VT.” reads the analysis published by the experts.
Once infected the system, the backdoor connects to the command and control (C&C) server to register the machine, it gains by using cron and an internal mutex, in this way only one instance remains alive at all times.
The backdoor supports the following commands:
- newtask – to execute arbitrary code, download and execute a file, kill or uninstall a program, and send updated fingerprint data;
- notask – sleep for 3 seconds and ask for additional command;
- newerconfig – to update the downloaded miner configuration file.
The backdoor uses a python script to scan and infect other Linux servers within internal and external subnets, it is also able to carry out brute-force admin panels.
The script attempts to exploit the following RCE vulnerabilities in the targeted servers:
- CVE-2012-0874: JBoss Enterprise Application Platform Multiple Security Bypass Vulnerabilities
- CVE-2010-1871: JBoss Seam Framework remote code execution
- JBoss AS 3/4/5/6: Remote Command Execution (exploit)
- CVE-2017-10271: Oracle WebLogic wls-wsat Component Deserialization RCE
- CVE-2018-2894: Vulnerability in the Oracle WebLogic Server component of Oracle Fusion Middleware.
- Hadoop YARN ResourceManager – Command Execution (exploit)
- CVE-2016-3088: Apache ActiveMQ Fileserver File Upload Remote Code Execution Vulnerability.
Further researches made by the experts allowed the experts to find liteHTTP GitHub project that has some modules similar to the SpeakUp Trojan.
“SpeakUp`s obfuscated payloads and propagation technique is beyond any doubt the work of a bigger threat in the making. It is hard to imagine anyone would build such a compound array of payloads just to deploy few miners.” Check Point concludes.
“The threat actor behind this campaign can at any given time deploy additional payloads, potentially more intrusive and offensive,”