San Francisco, CA – At the RSA Conference 2020, Gary Berman and I had the privilege of interviewing some of the top executives in the cybersecurity Community about what concerns weighed on their minds, regarding the state of the industry, and the challenges facing the digital world.
Overall, the common theme is that the InfoSec Community is facing an uphill battle in the never-ending fight to defend against malicious cyber attacks. “You see all this money getting pumped into solutions, and yet, we are just not winning,” says David Burg, principal cybersecurity leader for the Americas at EY. “I work for some of the biggest and most sophisticated companies in the world, and the problems that we see around cybersecurity – the failures they’re working to fix – I’m very surprised that, here in 2020, we don’t have this thing solved.”
The attack surface is expanding at an alarming rate, and security solutions companies are clamoring to stay at par with the rapidly developing technology and devices, as well as skyrocketing global usage. “There’s been an exponential increase in the attack surface area,” exclaims Srini Subramanian, principal and State sector leader at Deloitte. “The [variety] of ways for an attacker to get in are radically larger than they were a year, two years, five years ago. The reason is that ‘cyber’ permeates every aspect of business now.”
When it comes to enterprise security, the most prevalent issue revolves around phishing attacks. “We need to help our customers with phishing,” says Russ Mohr, Director of Sales Engineering at MobileIron. “We need to help them make the right decision, because they may not have 15 minutes to do the research. So, when they click on that phishing link, I want to be able to examine that link, and we’re going to block you before you go to this malicious website.”
Once you delve into the proverbial rabbit hole of supply chain risk, it’s hard not to be overwhelmed with anxiety. “The fact that we can’t control what happens outside of our organizations – that future supply chain – that’s what we really need to start thinking about,” says Jennifer Bisceglie, CEO at Interos, a cutting-edge supply chain risk management company that uses A.I. to constantly evaluate enterprise supply chain vulnerabilities in real-time. “It’s too dynamic, you can’t do this with people, and the faster we understand who we’re connected to [via supply chain relationships] and what that really means, the better off we’ll be from a global business standpoint.”
Cyber attacks come in all shapes and sizes, and from all manner of groups and individuals. However, it may be surprising to some, that not all damaging attacks are for-profit. “I call them ‘graffiti hackers,’” says Tom Kelly, CEO at ID Experts. “It’s a person that does it because they can! They’re not looking for money. They’re not really looking to disrupt or do harm. They’re just looking to do it… but, in the process, they might create a trail of harm.”
One of the major problems facing businesses is the multitude of legacy systems that create unnecessary vulnerabilities. “Any entity that has legacy platforms and systems, you can’t just go out and generally maintain them very well, from an IT perspective,” according to Bob Huber, a chief information security officer at Tenable. “You can’t catch them. You can’t update them. You can’t just deploy new systems. It’s very common across the industry that those platforms are just ripe targets because of their inability to be maintained.”
The perpetual stress associated with defending against cyber attacks is best encapsulated by Russell Jones, US Product Security Leader, Deloitte Risk & Financial Advisory, “It’s an asymmetric problem… [malicious hackers] just need to get it right once, while we have to defend it effectively every time for our clients.”
The pressure is mounting, as the speed of business continues to accelerate, and security systems are viewed as a hindrance rather than a necessary component of the business process. “A lot of organizations are going through digital transformation, so they want to get products out faster to their stakeholders and clients,” says Vikram Kunchala, Senior Manager of Technology Risk at Deloitte. “Security is always seen as the cop with the radar gun, as opposed to a member of the pit crew.”
The emergence of 5G is going to expand attack surfaces exponentially. “Everything will have the potential to be internet-enabled, which means every one of those devices needs ability management, patch management, user access control, data protection, and security,” according to Cody Cornell, Founder, and CEO at Swimlane. “It’s like going from [caring for] two kids, to suddenly, I have 20 kids, and your life changes in that moment!”
All of these tectonic shifts are giving rise to concerns. Chris Eng, Chief Research Officer at Veracode ponders, “Can we keep pace with speed that we need to go? I mean, development has gotten a lot faster, and if we, as a security industry don’t adapt to that, then we will get left behind.”
The key to overcoming the myriad challenges before us lies in effective communication, between industry peers, as well as to end-users. “We speak with 250,000 businesses every day, basically, so we’re getting the message [about changing standards of security assessments for companies and their supply chain providers] out now” Charlie Tupitza, Cybersecurity and Data Protection Lead of Americas Small Business Development Centers says, “I’m not going to sit around and worry about people losing lots of money because my job is to make them aware, and do something actionable!”
Impactful communication can come in various forms. “The mindset of security, by and large, is fear-based, and that bothers me,” declares Matt Glenn, Vice President of Product Management at Illumio. “It should be opportunity-based like you have the opportunity to do the right things. I don’t want people to be scared into doing things, I want people to be enticed into doing the right things.” He adds, “What keeps me up at night is people being so afraid – paralyzed by fear – that they don’t do anything!”
Another challenging aspect of communication centers around generational gaps. “We’re working [across] multiple generations,” says Lise Lapointe, CEO & President of Terranova Security. “We have [end-users] from 25 years old to 60 years old, and we have to address them in different ways. So, we need to get the content to the user in the way they want to receive it, and not in a way that is standardized for everybody.”
When it comes down to brass tacks, the number one concern regarding cybersecurity is focused on economic (monetary) risk. “I would say [what keeps me up at night is] the monetary damage and the monetary risk,” according to Oliver Friedrichs, Vice President of Products at Splunk. “The credit cards are relatively safe, but your bank account – when that money gets wired out by accident or by an adversary – it’s gone!”
In order to protect against financial losses, many enterprises and government entities rely on Cyber Insurance providers to mitigate monetary damages from a breach. “In the last 18 months, about two-thirds of all ransomware attacks were aimed at state and local government,” Andrew Morrison, Partner/Principal in the Advisory Practice of Deloitte reports. “We believe there are a couple of reasons for it. One is the prevalence of cyber insurance as an easy solution to paying the ransom.”
In addition, malicious hackers are empowered by the fact that the legal system has yet to adapt to the rapidly evolving cybercrime landscape. “[Cyber crimes] are almost never prosecuted, and it’s financially lucrative,” says Mike Wyatt, National Managing Principal – Identity Solutions Offering Leader at Deloitte. “So, until there’s a stopgap defense that changes the ecosystem, it’s going to continue.”
Some experts theorize that a monumental shift in prioritization is required, across all industries offering digital products to clients, in order to effectuate meaningful change. “If companies decide that their [customer’s data privacy] is as important as [theirs is],” proclaims Chris Olson, Co-Founder, and CEO at The Media Trust. “[Companies need to act like] it’s not about profit anymore. We’re all here for you. That’s true, probably in many things, but it’s absolutely not true for the digital asset.” He adds, “So, they need to start thinking about their websites and apps, and the way we’re talking about helping society. I think you’re going to see that [prioritization approach] get bigger and bigger.”
With so many stress factors in play, it is common to feel anxiety, especially given the uncertainty of what lies ahead. “You need to keep your wits about you in 2020,” concludes MobileIron’s Russell Mohr. “There are lots of angles of attack, but we need to do everything we can to enable our end-users to make the right decisions.”
Despite the myriad concerns pollinating the commercial world, at the end of the day the cybersecurity Community is full of optimism. “I tend to be kept up at night, not out of fear, but out of excitement for what’s coming next!” exclaims Lee Rosenwald, Security PR Manager at Intel. “As an A.I. practitioner, as a Machine Learning person, trying to take data and make sense of it, there’s been a lot of tension recently between unlocking the potential of A.I., but also want to maintain the privacy and security of the data that feed A.I. There are some really exciting techniques that my group is working on!”
The key takeaway from our discussions is that, while there are innumerable factors that could reasonably cause worry, or even panic, with regards to the present and future of data privacy and cybersecurity, there are even more reasons to celebrate. We are on the cusp of a transformational time in our existence, as a species. For sure, there will be aches and pains associated with this evolutionary leap, but the exponential expansion in our capabilities to learn, communicate, explore, and innovate will propel us into the next frontier of humanity, and grant us the ability to aim higher than we ever thought possible.
 Olivier Vallez, JD, MBA – Lead Writer/Cybersecurity Reporter
Olivier Vallez, JD, MBA – Lead Writer/Cybersecurity Reporter
Olivier Vallez is a contributing writer for Cyber Defense Magazine, covering various cybersecurity topics and events. He is the Head of Business Development at The CyberHero Adventures: Defenders of the Digital Universe, a groundbreaking comic platform that distills complex cybersecurity information into a fun and engaging superhero stories and makes cyber hygiene easy-to-understand for non-technical people.
 Gary Berman, Cybersecurity Reporter
Gary Berman, Cybersecurity Reporter
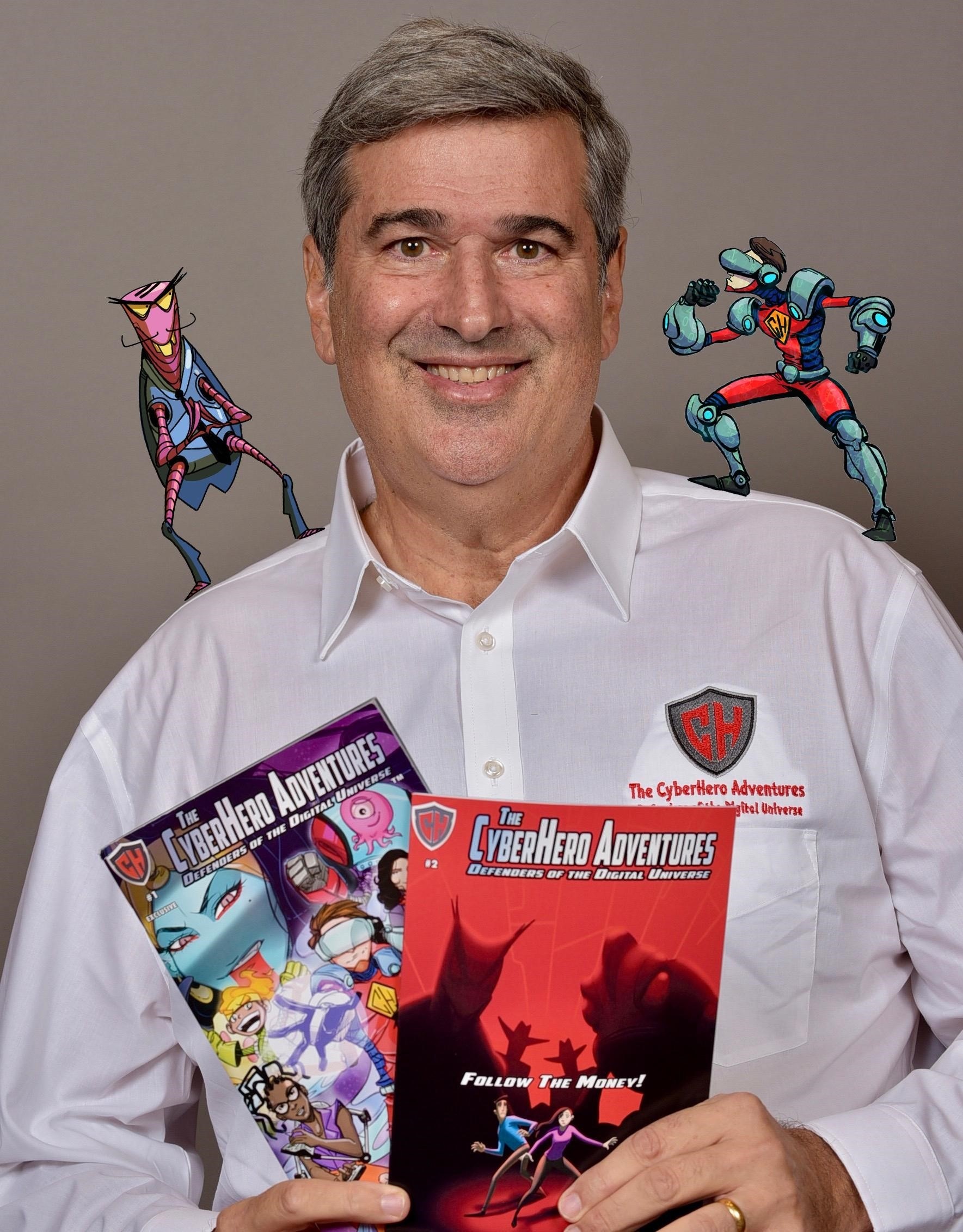
Gary Berman is a contributing reporter for Cyber Defense Magazine. He was the victim of a series of insider hacks for several years until he made the pivot from victim to advocate. He is creator and CEO of The CyberHero Adventures: Defenders of the Digital Universe, a groundbreaking comic series that distills complex cybersecurity information into entertaining and educational superhero stories, making cyber hygiene accessible for non-technical people.


