Experts discovered a new Windows info-stealer, named PyMICROPSIA, linked to AridViper group that is rapidly evolving to target other platforms.
Experts from Palo Alto Networks’s Unit 42 discovered a new Windows info-stealing malware, named PyMICROPSIA, that might be used soon to also target Linux and macOS systems.
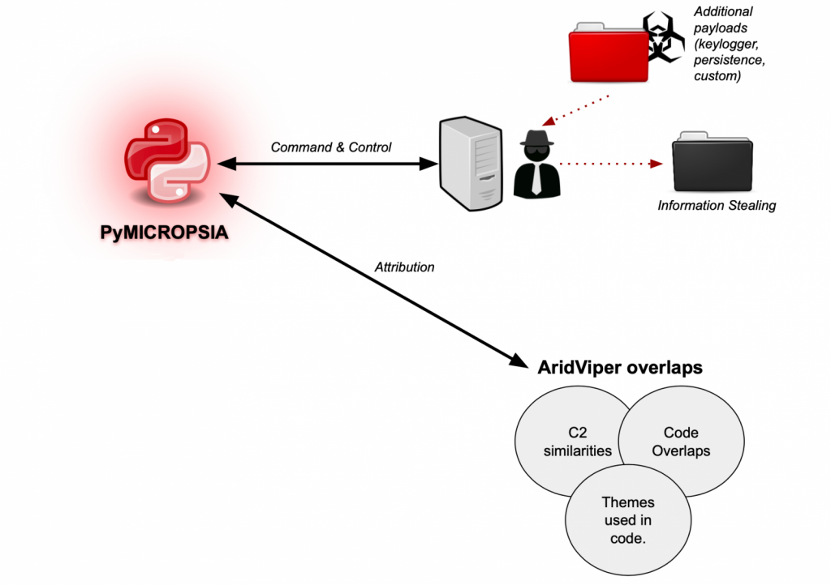
Experts spotted the PyMICROPSIA info stealer while investigating attacks of the AridViper group (also tracked as Desert Falcon and APT-C-23). AridViper is an Arabic speaking APT group that is active in the Middle East since at least 2011.
PyMICROPSIA is Python-based, its Windows binary is created using PyInstaller, but experts found evidence its authors are extending its capabilities to infect multi-platform.
PyMICROPSIA supports multiple functionalities, including:
- File uploading.
- Payload downloading and execution.
- Browser credential stealing. Clearing browsing history and profiles.
- Taking screenshots.
- Keylogging.
- Compressing RAR files for stolen information.
- Collecting process information and killing processes.
- Collecting file listing information.
- Deleting files.
- Rebooting machine.
- Collecting Outlook .ost file. Killing and disabling Outlook process.
- Deleting, creating, compressing and exfiltrating files and folders.
- Collecting information from USB drives, including file exfiltration.
- Audio recording.
- Executing commands.
PyMICROPSIA communicated with C2 with HTTP POST requests, it uses different Uniform Resource Identifier (URI) paths and variables that depend on the functionality invoked.
The researchers noticed several code branches in the code for C2 communication, some of them will never be executed when responses are processed, a circumstance that suggests the malware is under active development.
For the first time, the sample analyzed by Unit 42 researchers includes snippets checking for other operating systems, likely the threat actors are expanding their operations.
“PyMICROPSIA is designed to target Windows operating systems only, but the code contains interesting snippets checking for other operating systems, such as “posix” or “darwin”.” reads the analysis published by Palo Alto Networks. “This is an interesting finding, as we have not witnessed AridViper targeting these operating systems before and this could represent a new area the actor is starting to explore.”
Experts don’t exclude that the checks might have been introduced by vxers copy-pasting code from other ‘projects.’
PyMICROPSIA uses Python libraries to implements multiple operations, including data theft, Windows process and systems interaction.
Experts also documented a keylogging capability implemented using the GetAsyncKeyState API as part of a separate payload. The malware also uses another payload to gain persistence by dropping a .LNK shortcut in the Windows Startup folder of the infected Windows machine.
PyMICROPSIA is also able to achieve Persistence via regular methods, including via registry keys.
“AridViper is an active threat group that continues developing new tools as part of their arsenal. PyMICROPSIA shows multiple overlaps with other existing AridViper tools such as MICROPSIA.” concludes the analysis. “Also, based on different aspects of PyMICROPSIA that we analyzed, several sections of the malware are still not used, indicating that it is likely a malware family under active development by this actor.”