Did you know that only 4% of CISOs have real-time visibility into runtime vulnerabilities in containerized production environments (https://www.dynatrace.com/news/blog/runtime-vulnerability-management-still-vexing-organizations/)? According to Gartner, by 2025, over 75 percent of organizations will directly or indirectly monetize APIs. Gartner believes that by 2024, API abuse and related data breaches will nearly double. Security company Checkpoint found that there were a whopping 830,000 attack attempts made within 72 hours of revealing the Log4j vulnerability.
Enter THREATX to help you defend the cloud workloads powering your digital transformation from advanced runtime threats.
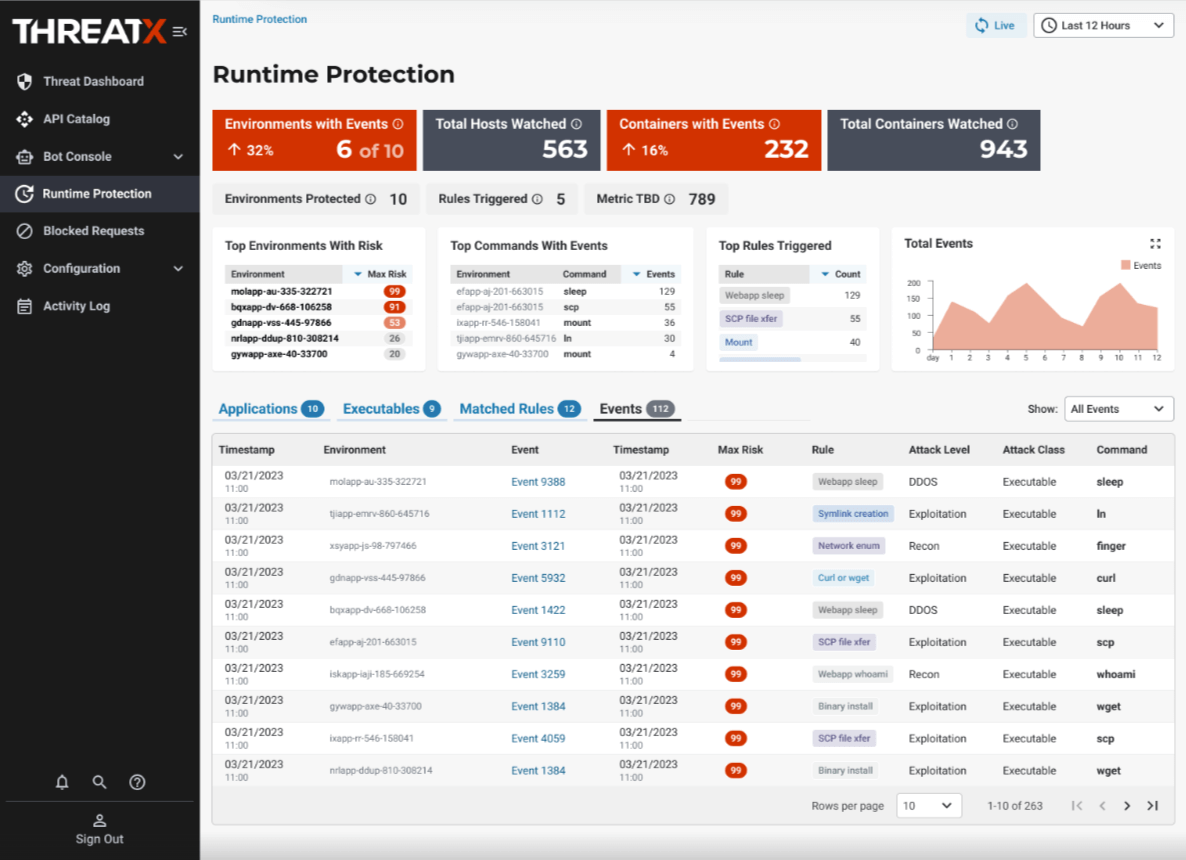
THREATX is managed API and application protection that protects against all threats, including DDoS attempts, bot attacks, API abuse, exploitations of known vulnerabilities, and zero-day attacks. THREATX breaks through the crowded cybersecurity industry because it doesn’t just identify threats, but blocks them in real time with accurate, risk-based blocking. It protects APIs and apps from the edge to the runtime environment and surrounds its platform with a Protection-as-a-Service team that acts as an extension of security teams.
THREATX onboards most sites to its platform in less than 15 minutes.
THREATX is unique in its ability to not just identify threats to APIs and applications, including botnet and DDoS attacks, but to block them, in real time. All the current stand-alone API security products are observability solutions – they tell you about vulnerabilities or attacks after the fact – then teams have to take that data and enter it into a separate solution (usually a WAF) in order to block – this process is time consuming and labor intensive, and again, after the fact.
“THREATX has been a game changer for my team and me,” said Steve Liu, SELCO Community Credit Union Director of IT, “and has provided an additional layer of security for our members. We were all taking turns working evenings and weekends, and the need for that stopped.”
In addition, THREATX is also the only API and application protection solution with the ability to protect both at the edge and at runtime. Many attackers now prioritize finding backdoors – often by exploiting vulnerabilities in running applications – to circumvent edge and perimeter defenses. Deployed as a sidecar container within a Kubernetes environment, THREATX Runtime API and Application Protection (RAAP) leverages extended Berkeley Packet Filter (eBPF) technology to enable deep network flow and system call inspection, process context tracing, and advanced data collection, profiling, and analytics.
APIs and apps are becoming attackers’ target of choice, and they’re having great success outsmarting most security solutions. With attackers moving at lightning speed, blending together different attack types, and using huge botnets to evade security controls, security teams are struggling to keep up.
The THREATX managed API and application protection platform is uniquely designed to help teams in this battle. THREATX doesn’t just identify threats to APIs and applications, but it blocks them, in real time. In addition, THREATX is the only API and application protection solution with the ability to protect both at the edge and at runtime, to defend against attacks against running applications.
Finally, “THREATX takes the pressure off security teams with our protection-as-a-service offering – acting as an extension of their team and a second set of eyes, we give security teams peace of mind, and their nights and weekends back,” said Gene Fay, CEO, THREATX. Learn more about them at https://www.threatx.com/
About the Author
 Gary Miliefsky is an internationally recognized cybersecurity expert, bestselling author and keynote speaker. He is a Founding Member of the US Department of Homeland Security, served on the National Information Security Group and served on the OVAL advisory board of MITRE responsible for the CVE Program. He founded and is the Publisher of Cyber Defense Magazine since 2012. Visit Gary online at: https://www.cyberdefensemagazine.com/
Gary Miliefsky is an internationally recognized cybersecurity expert, bestselling author and keynote speaker. He is a Founding Member of the US Department of Homeland Security, served on the National Information Security Group and served on the OVAL advisory board of MITRE responsible for the CVE Program. He founded and is the Publisher of Cyber Defense Magazine since 2012. Visit Gary online at: https://www.cyberdefensemagazine.com/