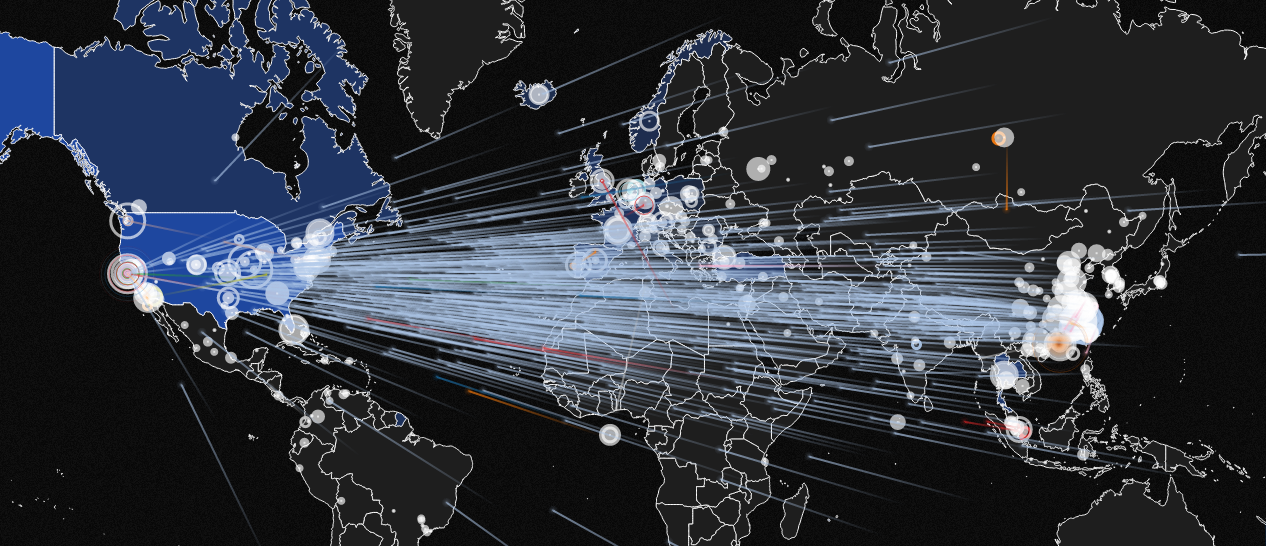
Recently a group of cybercriminals calling itself Phantom Squad unleashed a digital extortion scheme targeting businesses across the US, Europe and Asia. In the extortion notes the group threatened to take down the companies’ websites with a distributed denial of service (DDoS) attack, unless the targets paid a ransom of .2 bitcoins (about $780 today, though bitcoin value fluctuates fairly significantly on a daily basis).
Phantom Squad is most well-known for its attacks on gaming networks like Xbox and Steam. But this latest round of extortion notes targeted specific businesses, and were riddled with grammar errors, leading some experts to conclude the threat is the work of a copycats. While it’s hard to know if this is the real Phantom Squad or imposters hoping to capitalize on the group’s notoriety, one thing is certain: it’s time to rethink your DDoS defenses.
When there is heightened risk of an attack, organizations that cannot easily detect and differentiate performance anomalies from potential security events can inadvertently announce themselves as soft targets. One key indicator that an attack might be looming is the appearance of short traffic spikes leading up to the time period when attackers threaten they are going to strike. Cybercriminals perform reconnaissance against prospective targets to gauge reaction, defense strength and to understand a target’s security posture.
To ensure your organization has appropriate DDoS mitigation mechanisms in place, here are some important questions you should ask:
- What layers of protection do I have in place? Because no single protection is failsafe, the answer to this question will help an organization understand the methods and technologies being used to protect its site.
- What is our response time? Even the largest cloud providers often have surprisingly slow response times. Smaller organizations in particular should ensure that they won’t be put at the bottom of a priority list in the event of attack, making their likely response times even longer.
- How quickly can we determine the difference between an attack and a performance problem? Detection is essential and the speed in which protection can be enacted is key to reducing the risk of customer-facing, or business-threatening, impact.
- How variable is my cost of prevention? If I’m hit with a really big attack, will the mitigation costs spike to the point that I can’t afford them?
- Where are the DDoS mitigation facilities supporting me located globally? This helps organizations understand if DDoS mitigation capabilities comply with the various regulations that vary by country.
If you don’t know the answers, or if you aren’t confident the answers are sufficient to protect your organization from the havoc of a successful DDoS attack, improving your DDoS mitigation capabilities should be your first priority. We’ve got tips on how to do just that here.
About the Author
Joe Loveless is Neustar’s Security Solutions Director of Product Marketing with a focus on helping companies better protect their digital presence to better serve their customers. He has more than 25 year of experience in information technologies and services marketing working for and on behalf of Fortune 500 businesses including financial institutions, retailers, and other security sensitive industries. Loveless is currently leading Neustar’s initiative to bring the world’s largest DDoS mitigation network to market. His extensive experience includes marketing, management consulting, service implementations, and systems operations, particularly in enterprise management and information systems.