Security researcher Gjoko Krstic from Applied Risk discovered over 100 vulnerabilities that expose buildings to cyber attacks.
Security researcher Gjoko Krstic from Applied Risk discovered over 100 vulnerabilities in management and access control systems from four major vendors.
An attacker can exploit the vulnerabilities to gain full control of the vulnerable products and access to the devices connected to them.
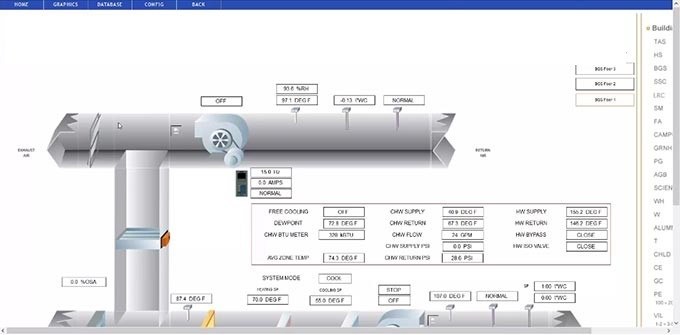
Krstic conducted a year-long study on building management (BMS), building automation (BAS) and access control products from Nortek, Prima Systems, Optergy, and Computrols. The experts analyzed several products, including Computrols CBAS-Web, Optergy Proton/Enterprise, Prima FlexAir, and two Nortek Linear eMerge products.
The expert discovered over 100 security flaws, including default and hardcoded credentials, command injection, cross-site scripting (XSS), path traversal, unrestricted file upload, privilege escalation, authorization bypass, clear-text storage of passwords, cross-site request forgery (CSRF), arbitrary code execution, authentication bypass, information disclosure, open redirect, user enumeration, and backdoors.
Some of the flaws, rated as ‘critical,’ could be exploited by an unauthenticated attacker to take full control of the vulnerable systems.
The extent of the flaw is wide, according to data collected by Krstic during the study, the vulnerabilities could impact up to 10 million people and 30,000 doors at 200 facilities.
Once hacked vulnerable systems, attackers could steal personal information and conduct a wide range of malicious activities, including lock or unlock doors and gates, control elevator access, trigger alarms, intercept video surveillance streams, and manipulate HVAC systems and lights, disrupt operations.
“It is possible to identify exposed systems using search engines like Shodan, and it is feasible to scan the entire IPv4 internet.” reads the analysis published by the experts related to Computrols CBAS-Web 18.0.0
Krstic presented the findings of his study at SecurityWeek’s ICS Cyber Security Conference held in Singapore.
Experts at Applied Risk published security advisories for each of the impacted products, they plan to release technical details for each flaw in June.
Applied Risk confirmed that all of the impacted vendors, except for Nortek, already released security updates to address the issued in their products.
According to SecurityWeek, Nortek already patched the issued identified by Applied Risk despite the company did not receive the actual details of the flaws.