SOVA is a new Android banking trojan that targets banking applications, cryptocurrency wallets, and shopping apps from the U.S. and Spain.
Researchers from cybersecurity firm ThreatFabric have spotted in the beginning of August a new Android banking trojan, dubbed SOVA, that targets banking applications, cryptocurrency wallets, and shopping apps from the U.S. and Spain. The name SOVA comes from the Russian word for owl.
The malware allows attacker to gather sensitive data from infected devices, including banking credentials and PII.
The banking trojan implements multiple harvesting capabilities, the malicious code is able to steal credentials and session cookies leveraging web overlay attacks, logging keystrokes, hiding notifications, and through clipboard highjacking.
The mobile malware is currently in development and testing phase, threat actors will likely implement other features to conduct DDoS and Ransomware attacks in future.
“Like many others, S.O.V.A. is also taking a page out of traditional desktop malware, confirming a trend that has been existing for the past few years in mobile malware. Including DDoS, Man in the Middle, and Ransomware to its arsenal could mean incredible damage to end users, in addition to the already very dangerous threat that overlay and keylogging attacks serve.” reads the analysis published by ThreatFabric. “Regarding the development, S.O.V.A. also stands out for being fully developed in Kotlin, a coding language supported by Android and thought by many to be the future of Android development.”
At the time of the publishing of report, ThreatFabric researchers identified three samples of S.O.V.A., two related to first iteration of the malware, and the last one being the newer release.
The authors of the SOVA banking Trojan have been advertising the product on hacking forums, in July they were looking for testers for their malicious code.
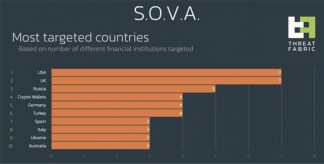
The country distribution of the targets shows that most of the infections were in the US, the UK and surprisignly in Russia.
“However, the author behind this bot clearly has high expectations for his product, and this is demonstrated by the author’s dedication to test S.O.V.A. with third parties, as well as by S.O.V.A.’s explicit feature roadmap.” concludes the analysis. “The current version of S.O.V.A. is capable of stealing credentials and session cookies through overlay attacks, keylogging, hiding notifications, and manipulating the clipboard to insert modified cryptocurrency wallet addresses. If the authors adhere to the roadmap, it will also be able to feature on-device fraud through VNC, DDoS capabilities, Ransomware, and advanced overlay attacks. These features would make S.O.V.A. the most feature-rich Android malware on the market and could become the ‘new norm’ for Android banking trojans targeting financial institutions.”
Follow me on Twitter: @securityaffairs and Facebook
 Pierluigi Paganini
Pierluigi Paganini
International Editor-in-Chief
Cyber Defense Magazine


