According a new report the popular Naikon APT group is actually backed by the China’s PLA Unit 78020, a firm traced it through online activity.
Ge Xing, also known as “GreenSky27,” is the name of a the alleged member of the People’s Liberation Army unit 78020, a group of Chinese state-sponsored hackers. The man was identified by a joint investigation conducted by the ThreatConnect and Defense Group Inc, Ge Xing and his colleagues gather intelligence from political and military sources to advance China’s interests in the South China Sea.
“ThreatConnect, in partnership with Defense Group Inc., has attributed the targeted cyber espionage infrastructure activity associated with the ‘Naikon‘ Advanced Persistent Threat (APT) group to a specific unit of the Chinese People’s Liberation Army (PLA),” the security intelligence firm explains. “Our assessment is based on technical analysis of Naikon threat activity and native language research on a PLA officer within Unit 78020,”
The publication of the findings of the investigation coincides with the official visit of the Chinese President Xi Jinping in the US, he is firmly denying any involvement of the Chinese Government in cyber espionage campaigns recently uncovered by security firms.
The control over the South China Sea is strategic for the Chinese Government due to the intense commercial activity in the area.
“The South China Sea is seen as a key geopolitical area for China,” explained Dan Alderman, deputy director of DGI. “With Naikon, we see their activity as a big element of a larger emphasis on the region and the Technical Reconnaissance Bureau fitting into a multisector effort to influence that region.”
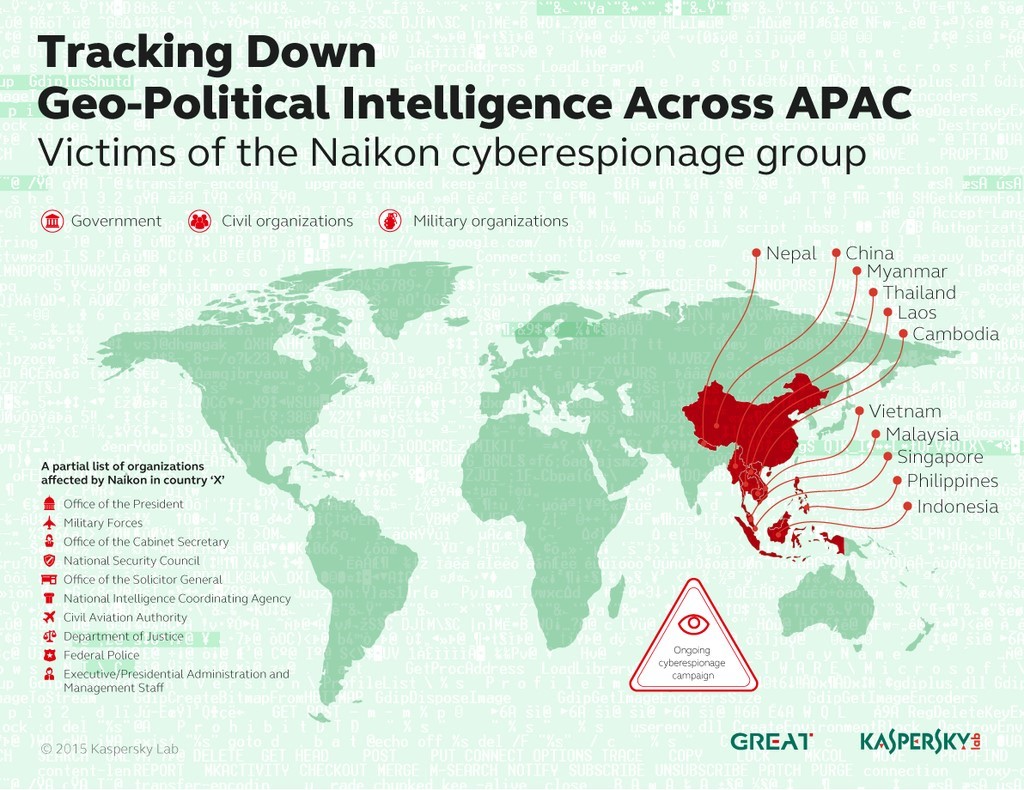
A report published by the ThreatConnect and Defense Group Inc. links the PLA 78020 to the Naikon APT group, which is one of the Asian largest APT gangs that has been active for several years. The missions of the Naikon APT targeted entities in various industries including governments and the military, the hacking crew targeted diplomats, law enforcement, and aviation authorities in many Asian countries such as the Philippines, Malaysia, Cambodia, and Indonesia. Naikon is the group which was involved in a cyber espionage campaign shortly after Malaysia Airlines Flight MH370 disappeared. Recently the group engaged a hacking dispute with another APT dubbed Hellsing.
In May, Kaspersky Lab published a detailed report on the Naikon APT group and its cyber espionage operations. According to the experts the group uses advanced hacking tools.
The Naikon APT group carried out surgical spear phishing attacks against its targets, the hackers relied on Word or Office documents to trigger a buffer overflow in the ActiveX controls of a MSCOMCTL.OCX Windows library (CVE-2012-0158).
The exploit allows attackers to infect victims with RAT and establish a backdoor on the victim’s system.
Ge is not described as a simple military but as an academic. The researchers discovered that his location is the headquarters of the PLA technical reconnaissance bureau by analyzing his online activity.
“Doing this kind of biopsy, if you will, of this threat through direct analysis of the technical and non-technical evidence allows us to paint a picture of the rest of this group’s activity,” said Rich Barger, CIO and cofounder of ThreatConnect. “We’ve had hundreds of hashes, hundreds of domains, and thousands of IPs [related to PLA unit 78020]. Only looking at this from a technical lens only gives you so much. When you bring in a regional, cultural and even language aspect to it, you can derive more context that gets folded over and over into the technical findings and continues to refine additional meaning that we can apply to the broader group itself.”
The report also detailed a series of operational security mistakes made by Ge, such as embedding certain names in families of malware attributed to Naikon APT group. The Naikon group and elite PLA unit appears very close.
“If you look at where China is and how assertive they are in region, it might be a reflection of some of the gains and wins this group has made,” Barger said. “You don’t influence what they’re influencing in the region if you don’t have the intel support capabilities fueling that operational machine.”
Below are reported Key findings from the investigation.
- Analysis of historic command and control (C&C) infrastructure used consistently within Naikon malware for espionage operations against Southeast Asian targets has revealed a strong nexus to the city of Kunming, capital of Yunnan Province in southwestern China.
- The C&C domain “greensky27.vicp[.]net” consistently appeared within unique Naikon malware, where the moniker “greensky27” is the personification of the entity who owns and operates the malicious domain.
- Further research shows many social media accounts with the “greensky27” username are maintained by a People’s Republic of China (PRC) national named Ge Xing (葛星), who is physically located in Kunming.
Great work, Enjoy the Report!