“2FA to 5FA – What are the options available?”
By David Smith
Independent Consultant at Smart Card Institute
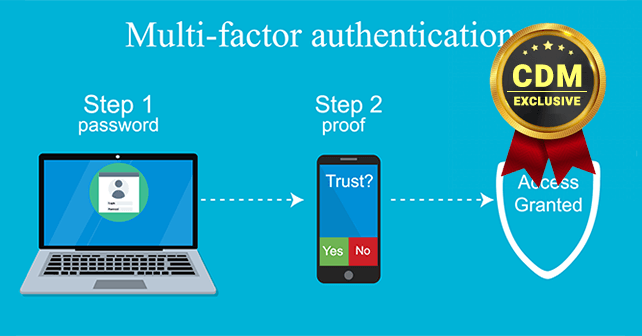
At some point of time, we have all used an OTP (One-time password) along with our password to successfully complete an online banking or financial transaction. While the OTP has provided an added sense of security that no one else besides you can authenticate that transaction, it heavily relies on the fact that the mobile device or token is in your possession during the transaction. The use of password + OTP for authentication is an example of Two-Factor Authentication (2FA). In order to ensure the authenticity of the user performing any transaction online or in-person, service providers and governing bodies are now emphasizing the use of multi-factor authentication mechanisms.
Multi-factor authentication has become a necessity to avoid the risk of identity theft caused by the use of weak or stolen user credentials, the possible vulnerability of systems and phishing attacks. As the name suggests, multi-factor authentication requires that a user provide 2 or more pieces of evidence as proof of his identity. The evidence provided should usually involve a mix of the below categories of factors.
- Knowledge factors – Something the user knows
- Possession factors – Something the user possesses
- Inherence factors – Something associated with the user’s body/personality.
- Location factor – Somewhere the user is
- Time factor – Time of the transaction.
We will now proceed to explore what are the different types of evidence that can be used to satisfy each of the above factors to successfully implement a multi-factor authentication system.
Knowledge Factors: Probably the most commonly used factor, something the user knows is usually his credentials like username, Email-Id, password, PIN, etc. Using an ATM card with PIN is an example of 2FA where one of the factors is the ATM card (which the user possesses) and the second is the PIN (which the user knows). Other examples for the use of knowledge factor include
- Security questions which are usually used when somebody wants to reset their password.
- CVV codes and expiry date on credit cards which are required during e-commerce transactions.
- Random One time passwords sent via SMS or emails when the user accesses a service
- The time-based one-time password generated by token devices based on a shared secret key and current timestamp using a cryptographic function.
Possession Factors: The oldest example of the possession factor is probably the key to a lock. The same principle continues to be used today in the digital age to control digital access. Smart cards are a commonly used possession factor today for digital access. They come in many forms like magnetic stripe and EMV cards used in credit/debit cards. RFID or NFC cards used in physical access control etc. Similar technology may be used in key fobs, wrist bands, etc. Hardware and software tokens are also used by many mobile banking applications to implement multi-factor authentication.
Inherent Factors: Biometric factors are commonly used to implement inherent factors. These include behavioral identifiers as well as physiological identifiers.
Behavioral identifiers include voice recognition, keystroke, and navigation patterns and engagement patterns. These rely on matching patterns of a person’s vocal characteristics, speed and pressure of typing and engagement with technology respectively. Voice recognition is typically used in call center/IVR applications while keystroke and navigation patterns are used when implementing remote multi-factor authentication.
Physiological identifiers include fingerprint, face and iris/retina scans. These make use of the unique patterns formed by a person’s fingerprints, face structure or retinal blood vessels/iris colors. They are commonly used to authenticate people on airports during immigration. Biometric payment cards are proposed to be the next step in security in the online/in-person payments industry.
Location factors: These usually check where the user is accessing the service from. Use of mobile phones has made it easier to track location. Example of implementation of location-based authentication is, when a user is within the office premise, he can connect directly to the corporate network through Wi-Fi or LAN. On the other hand, to access the corporate network over a VPN, a soft token is usually required.
Time Factor: Systems could have an inbuilt logic to check if the time of access is in line with the expected pattern. For example, a person may not be allowed to access a paid service from two geographically distant locations within a matter of minutes.
2FA is the most commonly used type of authentication and relies mostly on any two of the first 3 factors of knowledge, possession, and inherence. 3FA, 4FA, and 5FA using 1 of each type of factors are also implemented in special cases. Finally, it is important to note that the reliability of the mechanism used depends not only on which type of authentication is used but also on how it is implemented. A balance must also be maintained to ensure that users don’t feel confused or overburdened by the number of steps required to get access.
About the Author
 David Smith is a cryptographer with 12 years of experience in both the public and private sectors. His expertise includes system design and implementation with contact and contactless smart cards, smart card personalization, mobile payments, and general knowledge and experience with APAC market trends and consumer preferences. David occasionally consults with smart card companies at websites like Cardzgroup.com and you can be reached David online at Linkedin
David Smith is a cryptographer with 12 years of experience in both the public and private sectors. His expertise includes system design and implementation with contact and contactless smart cards, smart card personalization, mobile payments, and general knowledge and experience with APAC market trends and consumer preferences. David occasionally consults with smart card companies at websites like Cardzgroup.com and you can be reached David online at Linkedin