Organizations are delaying in patching Microsoft Exchange Server flaw (CVE-2020-0688) that Microsoft fixed with February 2020 Patch Day updates.
Organizations are delaying in patching Microsoft Exchange Server flaw (CVE-2020-0688) that Microsoft fixed with February 2020 Patch Day updates.
The CVE-2020-0688 flaw resides in the Exchange Control Panel (ECP) component, the root cause of the problem is that Exchange servers fail to properly create unique keys at install time.
The experts did not provide details on the threat actors that are exploiting the vulnerability, according ZDNet that cited a DOD source the attackers belong to prominent APT groups.
“Knowledge of a the validation key allows an authenticated user with a mailbox to pass arbitrary objects to be deserialized by the web application, which runs as SYSTEM.” reads the advisory published by Microsoft.
A remote, authenticated attacker could exploit the CVE-2020-0688 vulnerability to execute arbitrary code with SYSTEM privileges on a server and take full control.
Security experts Simon Zuckerbraun from Zero Day Initiative published technical details on how to exploit the Microsoft Exchange CVE-2020-0688 along with a video PoC.
The vulnerability impacts Microsoft Exchange 2010, 2013, 2016, and 2019.
Last week, cybersecurity firm Volexity warned that nation-state actors are attempting to exploit the CVE-2020-0688 flaw.
According to security firm Kenna Security, companies are very slow in addressing the vulnerability, less than 15% have already fixed it at the moment.
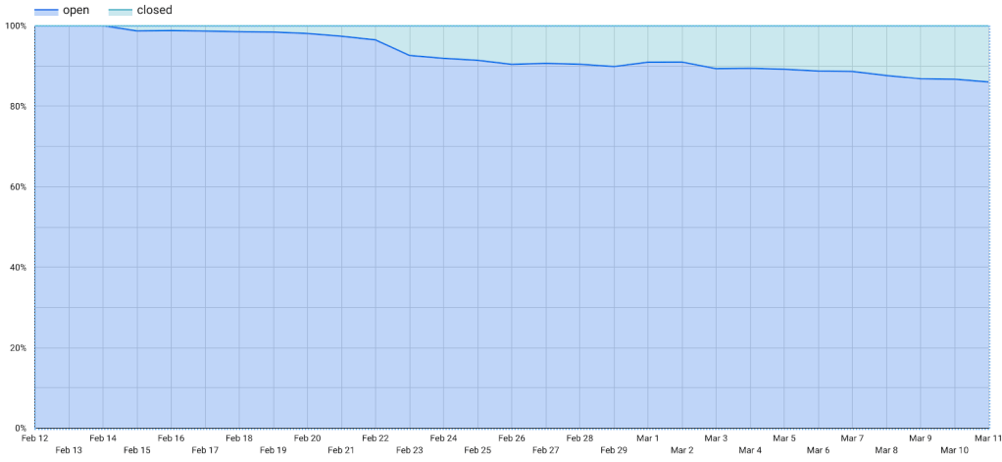
“In order to understand how remediation teams were doing against this critical vulnerability, we pulled a representative sample of remediation data, giving us the rate of open vs closed instances of the vulnerability. This was not encouraging. The vulnerability is currently less than 15% remediated.” reads the report published by Kenna Security.“Looking at the rate of open vs closed instances of the vulnerability, the security firm observed that remediation efforts are at less than 15% at the moment.”
The researchers working with the peers at BinaryEdge discovered 220,000 Outlook Web Access installs exposed on the Internet, most are 2013, 2016, and 2019.
The researchers determined that 74% of the servers are vulnerable, the remaining 26% are potentially vulnerable.
“How many of these are vulnerable? Using the inferred information – we can’t be 100% accurate since there’s no clear indicator that the patch was applied.” continues the report. “But, based on the underlying version, we can label as either “vulnerable” or “potentially vulnerable. ”After doing this labeling, we got the result: 74% vulnerable and 26% potentially vulnerable. This falls in line with the first analysis and is not particularly encouraging.”
Kenna Security recommends organizations to address the flaw as soon as possible or block access to ECP as mitigation.
“In most Microsoft-centric organizations, Exchange is a critical organization service, and thus, may be off-limits for normal monthly patching schedules.” concludes the report. “This fact, combined with the fact that the vulnerability exposes SYSTEM access on the server, and the fact that exchange stores credentials in memory in plain text, make this an incredibly attractive target,”.