Experts at Akamai discovered the Linux XOR DDoS Botnet, a malicious infrastructure used to run potent DDoS attacks against dozens of targets.
Security researchers have discovered a Linux Botnet, dubbed XOR DDoS or Xor.DDoS botnet, that is targeting gaming and education websites with potent DDoS attacks with reached 150 gigabytes per second of malicious traffic.
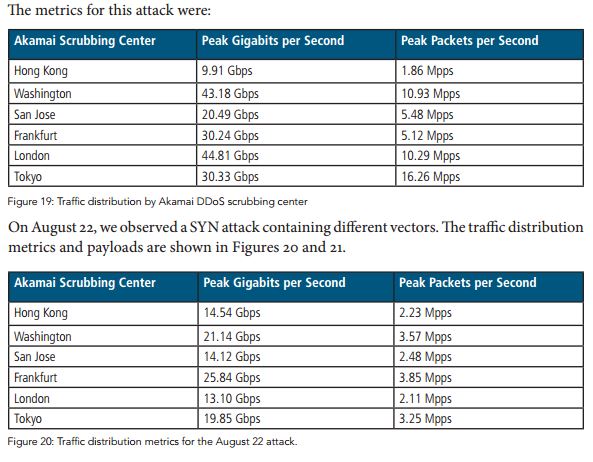
According to an advisory published by the content delivery network Akamai Technologies, the XOR DDoS botnet has targeted at least 20 websites each day, nearly 90 percent of the targets are located in Asia.
“Akamai’s Security Intelligence Response Team (SIRT) is tracking XOR DDoS, a Trojan malware attackers are using to hijack Linux machines to include within a botnet for distributed denial of service (DDoS) campaigns. To date, the bandwidth of DDoS attacks coming from the XOR DDoS botnet has ranged from a few gigabits per second (Gbps) to 150+ Gbps. The gaming sector is the primary target, followed by educational institutions. Akamai SIRT released a threat advisory this morning authored by Security Response Engineer Tsvetelin “Vincent” Choranov.” states the advisory.
“In short: Xor.DDoS is a multi-platform, polymorphic malware for Linux OS, and its ultimate goal is to DDoS other machines,” reported a post published by the Blaze Security blog. “The name Xor.DDoS stems from the heavy usage of XOR encryption in both malware and network communication to the C&Cs (command and control servers).”
The researchers observed that the attackers masquerade the IP addresses of the machines involved in the DDoS attack, in some cases they used IP spoofing techniques to make it harder for victims to defend their infrastructure from the attack.
The experts discovered that the XOR DDoS attacks rely on Linux machines that were compromised by cracking weak passwords used to protect the command shell.
Once the attackers have obtained the access to the Linux machine whey use root privileges to launch a script used to download and executes a malicious binary file.
“XOR DDoS is an example of attackers switching focus and building botnets using compromised Linux systems to launch DDoS attacks. This happens much more frequently now than in the past, when Windows machines were the primary targets for DDoS malware.” explained Stuart Scholly, senior vice president and general manager of Akamai’s Security Business Unit.
XOR DDoS isn’t the unique botnet composed of Linux systems recently discovered, other examples of Linux-based malware includes the Spike DDoS toolkit and the IptabLes and IptabLex malware that last year targeted Linux servers to run large-scale DDoS attacks.
“There are an increasing number of Linux vulnerabilities for malicious actors to target, such as the heap-based buffer overflow vulnerability found earlier this year in the GNU C library. However, XOR DDoS itself does not exploit a specific vulnerability.” explained the advisory published by Akamai.