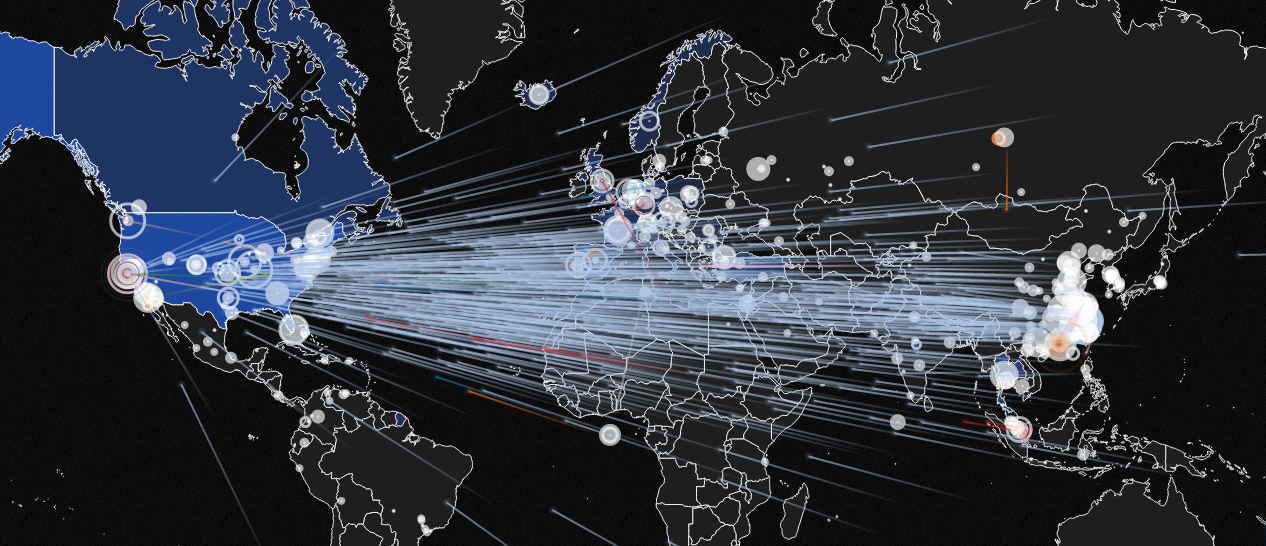
Security experts observed attackers launching a powerful LDAP DDoS, the new amplification method could peak Terabit-Scale attacks.
LDAP DDoS attacks are the novelty in the threat landscape, the Lightweight Directory Access Protocol (LDAP) protocol could be abused to power massive DDoS attacks.
The LDAP is an open standard application protocol for accessing and maintaining distributed directory information services over an Internet Protocol (IP) network.
The experts at the DDoS mitigation provider Corero Network Security confirmed that an LDAP DDoS attack has been already observed in a live incident. The attack leverages on a CLDAP zero-day vulnerability, a similar attack has been observed last week, and experts believe that could become another option in the arsenal of hackers in the wild.
Abusing the LDAP protocol it is possible to obtain an amplification factor of 46x, that in specific conditions could peak at 55x.
The experts from Corero explained that the attacker could send a query from a spoofed address (the victim address) to a vulnerable reflector supporting the Connectionless LDAP service (CLDAP).
The CLDAP service, then sends the response to the spoofed address, of course, the size of the response is much larger than the original query.
“In this case, the attacker sends a simple query to a vulnerable reflector supporting the Connectionless LDAP service (CLDAP) and using address spoofing makes it appear to originate from the intended victim. The CLDAP service responds to the spoofed address, sending unwanted network traffic to the attacker’s intended target.” reads a blog post published by Corero.
“Amplification techniques allow bad actors to intensify the size of their attacks, because the responses generated by the LDAP servers are much larger than the attacker’s queries. In this case, the LDAP service responses are capable of reaching very high bandwidth and we have seen an average amplification factor of 46x and a peak of 55x.”
LDAP DDoS attacks could cause serious damage, experts confirmed that they can peak at tens of terabits per second in volume of traffic.
“When combined with other methods, particularly IoT botnets, we could soon see attacks reaching previously unimaginable scale, with far-reaching impact. Terabit scale attacks could soon become a common reality and could significantly impact the availability of the Internet– at least degrading it in certain regions,” said Dave Larson, CTO/COO at Corero Network Security, explains.
[adrotate banner=”22″]