Exabeam’s ‘2020 State of the SOC Report’ offers peer-to-peer SOC comparisons
By Steve Moore, chief security strategist, and Samantha Humphries, senior product marketing manager, Exabeam
Security operations centers (SOCs) are on the frontlines in protecting businesses and government agencies against cyberthreats and attacks. Therefore, whether the organization has an in-house or outsourced SOC, it’s critical to gauge the effectiveness, given the importance it plays in the overall cybersecurity posture.
Exabeam’s 2020 State of the SOC Report allows organizations to compare their SOCs to those of their peers around the globe and determine common pitfalls, priorities, and ways to improve technology, staffing, employee happiness, and more. Highlights include:
This report is the Exabeam’s third annual comprehensive survey of cybersecurity professionals who manage and operate SOCs. Respondents include CISOs, CIOs, frontline security analysts, and security managers from the U.S., U.K., Canada, Germany, and Australia. The report covers a wide range of topics including basic SOC operations, hiring and staffing, operational processes, technology and finance, and budget.
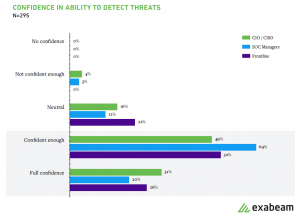
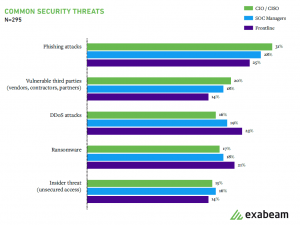
Key findings include that SOC leaders and analysts are confident in their ability to detect common security threats but do not agree on the threats. In addition, SOC leaders and frontline analysts do not agree on the most common threats facing the organization. SOC leaders believe that phishing and supply chain vulnerabilities are more important issues, while analysts see DDoS attacks and ransomware as greater threats.
However, threat hunting and the ability to remediate threats effectively stand out as critical skills that SOC personnel feel they lack. This gap may indicate that SOCs are overconfident in their ability to detect a full range of security threats.
Figure 1: Eighty-two percent of SOC professionals are confident in their ability to detect threats.
Figure 2: SOC leaders believe that phishing and supply chain vulnerabilities are more important issues, while analysts see DDoS attacks and ransomware as greater threats.
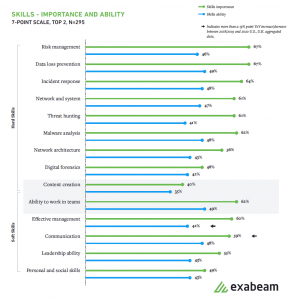
In last year’s report, respondents cited personal and social skills as the most critical soft skill for SOC employees. This year, however, 62% of respondents noted the ability to work in teams as the most important soft skill.
Figure 3: While hard skills remain critical, SOCs place emphasis on soft skills with the ability to work in teams taking precedence over formerly reported social ability.
The importance placed on teaming is an indication that SOC staff need to work in cohesive teams and often with staff from other teams. SOC members that work as a team are more apt to document processes to standardize tasks and train new employees, which is helpful both as teams grow or are reassigned.
Members of a SOC should not only improve teaming among their group, but also proactively strengthen their working relationship with other functional groups, including IT operations, NOC staff, and increasingly, DevOps. Working with these other groups helps to improve response time. More important, it will create a team that is responsive and able to adapt as the work environment shifts due to challenges like working with a distributed workforce and ensuring the right collaboration and communications tools and culture are in place.
The report also reveals a significant decline in the ability to do threat modeling in both the U.S. and U.K. SOCs. Threat modeling is the systematic approach to identifying and prioritizing potential security threats and designing countermeasures to prevent them. The data suggests threat modeling doesn’t have an agreed-upon standard, and most analysts perform it infrequently or not at all.
Additionally, the ability to conduct incident analysis and budget and resource allocation for both countries have declined from the previous year.
Figure 4: U.S. and U.K. SOCs reported significant declines in their ability to do threat modeling, incident analysis, and budget/resource allocation in YoY change.
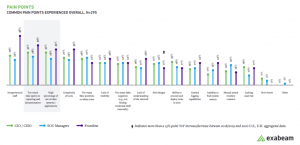
The findings also show that when asked to rate pain points, inexperienced staff and time spent on reporting/documentation were common issues for managers and frontline employees but not for executives.
Lending credence again to the statement, “you can’t protect what you can’t see,” senior leaders noted that the lack of visibility and not having a good list of assets were their most significant pain points.
Figure 5: Inexperienced staff and too much time spent on reporting and documentation continue to be pain points for SOCs in 2020.
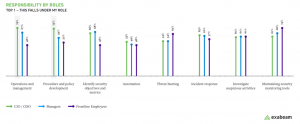
Traditionally, SOC teams have generally been responsible for two primary responsibilities — investigating suspicious activities and maintaining security tools. But over the years, the responsibilities of the SOC has increased to include other duties such as defining security metrics and incident response. Our report finds that staff at all levels share these responsibilities. However, there are a couple of differences.
CIOs and CISOs rank their responsibility for operations management as well as policy and procedure development highest. They also share other responsibilities with managers and frontline employees, including defining security objectives and metrics and incident response. Not surprisingly, maintaining security monitoring tools was noted as a critical responsibility for frontline employees.
Figure 6: SOC managers drive metrics specifically in operations and management and procedure and policy development.
Download the complete report to learn other points of interest that can help measure the effectiveness of your SOC and support you in your ongoing efforts to protect your organization.
About the Author
Senior Product Marketing Manager
Samantha has 20 years of experience in cybersecurity. She has defined strategy for multiple security products and technologies, helped hundreds of organizations of all shapes, sizes, and geographies recover and learn from cyberattacks, and trained anyone who’ll listen on security concepts and solutions. She authors articles for various security publications, and is a regular speaker and volunteer at industry events, including BSides, IPExpo, CyberSecurityX, The Diana Initiative, and Blue Team Village (DEFCON).”
Chief Security Strategist
Steve Moore is Vice President and Chief Security Strategist at Exabeam, helping drive solutions for threat detection and advising customers on security programs and breach response. He is the host of the “The New CISO Podcast” and a Forbes Tech Council member. Prior to Exabeam, Moore served as Staff VP of Cybersecurity Analytics at Anthem, a Fortune 30 healthcare company. Moore’s experience includes leading the investigation of state-sponsored cyberespionage campaigns, breach response, associated legal depositions, and client management. He’s passionate about cybersecurity, teamwork, and leadership excellence.