A couple of researchers demonstrated how to bypass vein based authentication using a fake hand build from a photo.
If you consider vein based authentication totally secure, you have to know that a group of researchers demonstrated the opposite at the Chaos Communication Congress hacking conference.
Vein based authentication scan invisible vein pattern (i.e. shape, size, and position of a user’ s veins) of the palm, back of the hand, fingers, etc, to identify the user.
The method of authentication is considered ultra-secure, it was also used by the German intelligence agency BND in the new headquarter building in Berlin.
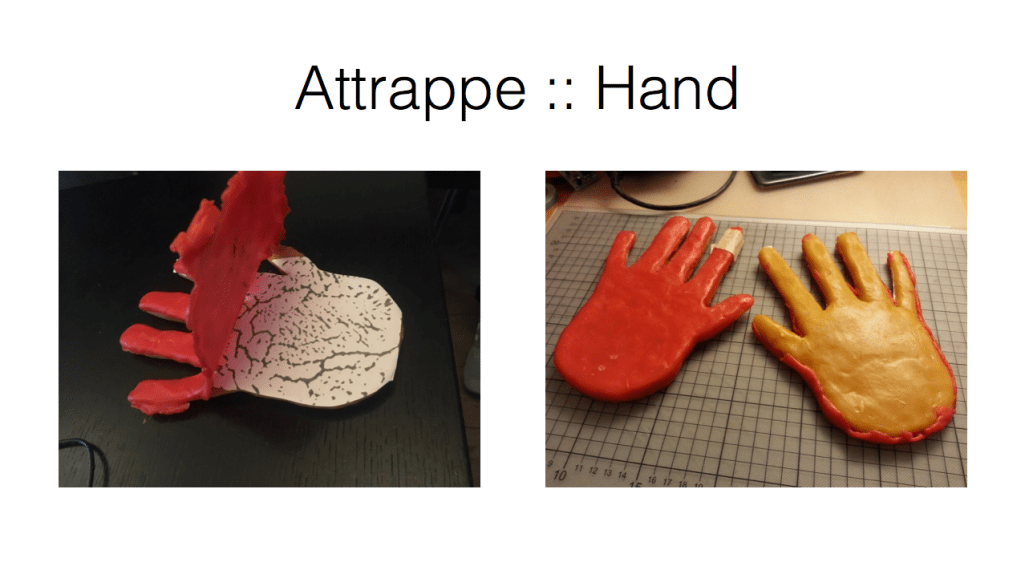
Researchers Jan Krissler (aka starbug) and Julian Albrecht at Chaos Communication Congress hacking conference, held in Leipzig, Germany, devised a way to bypass the vein based authentication by creating a fake hand out of wax.
“It makes you feel uneasy that the process is praised as a high-security system and then you modify a camera, take some cheap materials and hack it,” Krissler and Albrecht told Motherboard.
To build the fake hand out of wax, Krissler and Albrecht took photos of their vein patterns under the skin, then they used a converted SLR camera with the infrared filter removed. The experts explained that a threat actor could use this technique to take a photo of a hand from a distance of five meters. The security duo took over 2,500 pictures over 30 days to build a working hand of wax.
“It’s enough to take photos from a distance of five meters, and it might work to go to a press conference and take photos of them,” Krissler explained.
“When we first spoofed the system, I was quite surprised that it was so easy,” “Biometrics is always an arm race. The manufacturers improve their systems, the hackers come and break it and then it goes back on.”
The experts shared the details of their research to Fujitsu and Hitachi.
Researches warn that a persistent attacker could use the technique they tested to bypass vain based authentication used to protect restricted areas.