FireEye documented more than 1,500 vulnerabilities affecting ICS disclosed in the past 15 years, and some of them are still present.
Security of critical infrastructure is a pillar of the cyber strategy of any government, both the NIS directive and Warsaw NATO summit stressed the importance of a proper security posture to protect our systems from cyber attacks.
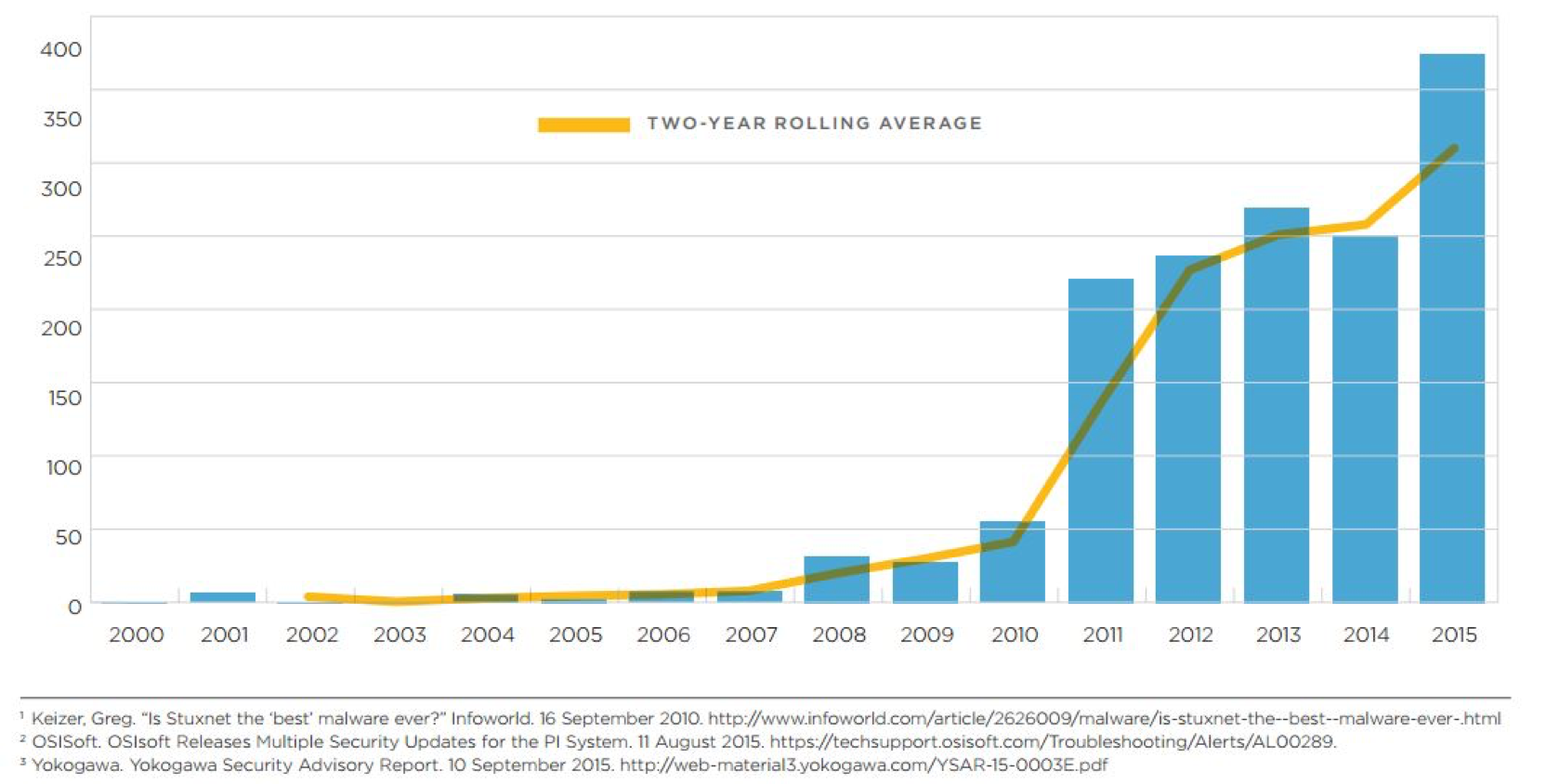
According to a new report published by FireEye, titled “Overload: Critical Lessons from 15 Years of ICS Vulnerabilities, the security firm has observed 1,552 flaws affecting ICS products of 123 vendors since 2000. The vast majority of the vulnerabilities documented by the experts was spotted after 2010, the year that cyber security expert link to the discovery of the cyber weapon Stuxnet.
The document published by FireEye reveals that in 2010 there were discovered 149 ICS vulnerabilities, in 2011 the number increased by 300 percent. From 2012 until 2014, the average number of ICS flaws increased by five percent year by year. The 2015 is considered the “Annus horribilis” for the ICSs, the experts observed a spike due to 92 security issues disclosed by two vendors.

“The discovery of Stuxnet in 2010 drove interest in industrial control systems (ICS) vulnerability research. FireEye iSIGHT Intelligence counted just 149 ICS vulnerability disclosures that were made between January 2000 and December 2010. Through April 2016, we have counted 1,552. We anticipate this upward trend will continue. ” states the report.
What about the future?
Experts at FireEye believe that the number of disclosed vulnerabilities will continue to rise in the coming years, likely with a similar trend (at an average of five percent per year), with occasional drops and spikes.
Giving a close look at the 801 vulnerabilities disclosed between February 2013 and April 2016, it is possible to note that 50 percent affected products at the second level of the Purdue ICS architectural model. These systems allow human operators to supervise and control the processes, attacks against level 2 systems represent a serious threat because can allow attackers to manipulate processes with unpredictable consequences.
“Most (58%) of the 801 ICS-specific vulnerability disclosures since February 2013 dealt with Level 2 (L2) in the simplified Purdue ICS architecture model, which describes how manufacturing devices interface with computers. We surmise that this is because L2 software is easier to obtain than L1 devices and is more familiar to a greater number of vulnerability researchers. However, adversary access to L2 alone is generally sufficient for at-will interaction with the controlled process.” continues the study.
How many zero-days?
According to the report, 33 percent of the flaws were zero-day vulnerabilities, and the bad news is that of 400 security issued discovered last year, more than 100 were unpatched when they were publicly disclosed.
“Vulnerability patching presents a significant challenge. Of the 1,552 total vulnerability disclosures we examined, 516 (33%) had no vendor fixes. The lack of vendor fixes and slow patch times for most industrial environments presents a significant opportunity for potential adversaries.”
Let me suggest to read this interesting study.