Trend Micro experts discovered a new strain of Point-of-Sale (PoS) malware dubbed FastPOS that implements a quick and efficient exfiltration technique.
Security experts at Trend Micro have spotted a new strain of PoS malware dubbed FastPOS that is able to quickly exfiltrate harvested data.
The malware was used by threat actors to target both enterprises and SMBs in several countries across the world, including the United States, Brazil, France, Japan, Hong Kong, and Taiwan.
The FastPOS malware is usually served via compromised websites, via VNC access using stolen credentials or brute-force attacks, or through a file sharing service.
“Take the case of this newly discovered PoS malware which is notable for its speed in how the information is stolen and sent back to attackers. We call this malware FastPOS, due to the said speed and efficiency of its credit card theft capabilities.” Trend Micro wrote in a detailed report on the FastPOS malware.
Like other PoS malware, FastPOS scrapes the memory of the infected device to steal payment card data and it also logs keystrokes, but different from other PoS malware it sends the harvested data immediately back to the C&C server that is hardcoded in the malware.
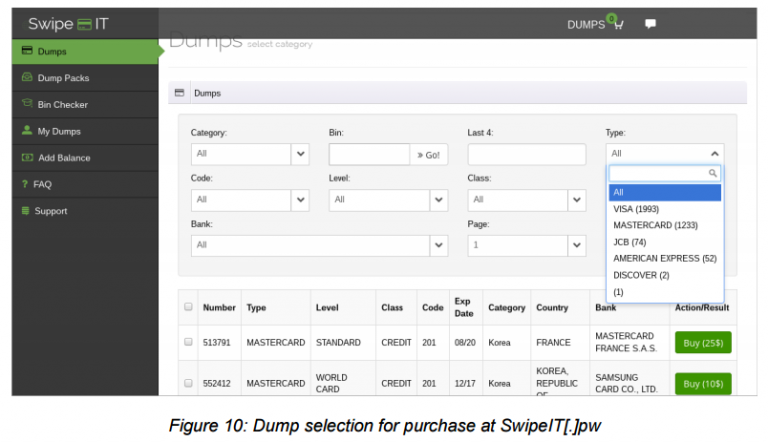
The C&C server also hosts a crime forum that specializes in selling payment card data.

The RAM scraping feature implemented by FastPOS relies on a custom algorithm that checks the card validity and the fact that the card can be used internationally and it does not require a PIN.
“The main RAM scraping process handled by the second thread and a custom algorithm is implemented in the following flow:
- Check field separator (‘=’ or ‘D’)
- Check first digit of the primary account number (aka, primary account number or PAN) (3,4,5,6)
- Check expiry year (not later than 2040)
- Check expiry month (no value above 12)
- Service code should be 201 or 101 (magnetic stripe card/IC card, PIN not required)
- Must pass Luhn validation
- Data after service code should be digits from 0-9 up to 16 characters, and ends with ‘?’ “
In order to avoid detection, FastPOS maintains log keystrokes in memory, without writing them on the disk, a technique already implemented by other malware like NewPosThings.
The keylogging feature collects several data including passwords, personal details, financial data and also the title of the window where the data has been entered.
The threat exfiltrates data leveraging an HTTP GET request instead of a POST request, which is the privileged choice for data stealer malware.
“One possibility is that the use of a GET command is designed to cause fewer suspicions – after all, this is the same command used when any browser retrieves a website,” continues Trend Micro.
As explained by the experts at Trend Micro, FastPOS could be very effective in targeting small organizations thanks its quick and efficient exfiltration technique.