Fansmitter is a new acoustic data exfiltration method devised by a group of researchers from Ben-Gurion University of the Negev.
We all know that air-gapped networks aren’t totally secure, in the past, many research groups have devised methods to steal data from computers disconnected from the Internet.
It is possible, for example, to exfiltrate data through the analysis of sound waves, heat emissions, and PC’s noises.
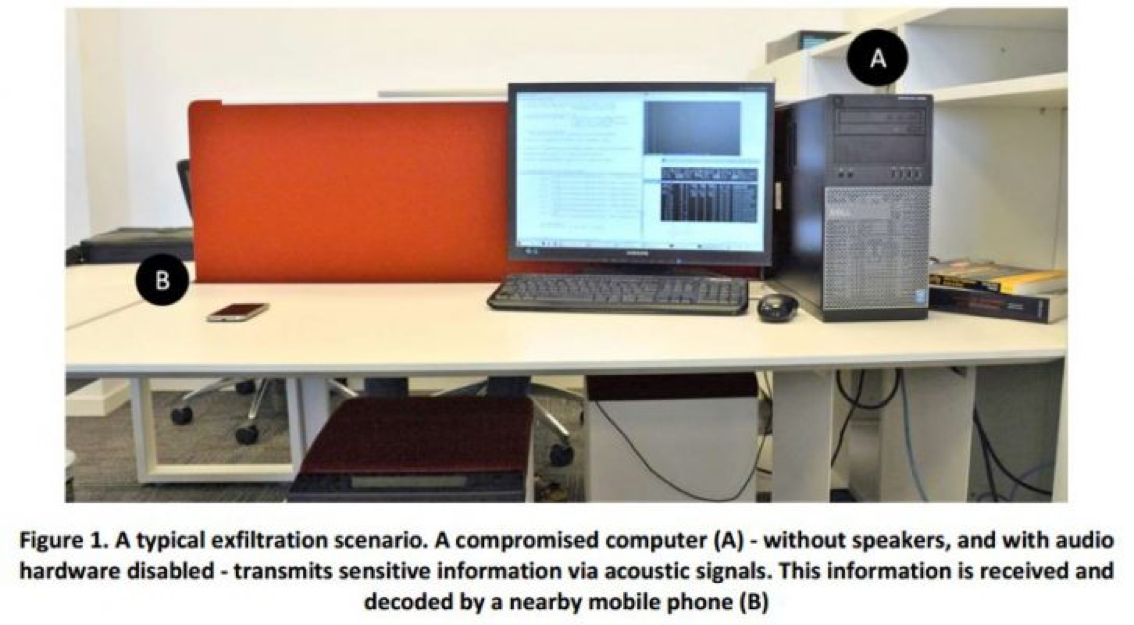
Now experts from Ben-Gurion University of the Negev have presented a new acoustic data exfiltration method that leverages on a mobile phone placed in the vicinity of the targeted machine to monitor the computer fans (i.e. CPU and chassis fans), for this reason, the method was called Fansmitter.
The malicious code developed by the researchers can use the device’s fans to exfiltrate data, with this method it sends out bits of data to the mobile phone or any other computer equipped with a microphone.
“Past research has demonstrated that malware can exfiltrate information through an air-gap by transmitting audio signals from the internal or external speakers of desktop computers.” reads the Fansmitter paper published by experts.
“Using Fansmitter attackers can successfully exfiltrate passwords and encryption keys from a speakerless air-gapped computer to a mobile phone in the same room from various distances,” researchers wrote in their paper. “Beyond desktop computers, our method is applicable to other kinds of audioless devices, equipped with cooling fans (various types and sizes of fans) such as printers, control systems, embedded devices, IoT devices, and more.”
The researchers were able to analyze the frequency and the strength of the acoustic noise emitted by fans that depend on revolutions per minute (RPM). The malicious code developed by the researchers is able to control the fan rotation producing specific noises that are associated with binary digits (0,1).
The noise produced by the fan is included in the 100-600 Hz range. This range of noise is audible by humans, so in order to avoid detection, the researchers can instruct the malware for transmitting data during hours when no one is in the room.
The experts used a common Dell desktop computer with CPU and chassis fans for their test session, noises were captured with a Samsung Galaxy S4 smartphone. The researchers also operated in the presence of other background noises produced by other computers in their lab and the air conditioning system.
Ladies and gentlemen … here are the results!
The researchers were able to transmit 3 bits per minute using low frequencies (1000 RPM for “0” and 1600 RPM for “1”) over a distance of one meter. Each character of a password or an encryption key could be exfiltrated in three minutes
Increasing the frequency in the Fansmitter it is possible to have better transfer rate, for example using a rotation range of 2000-2500 RPM the experts transferred 10 bits per minute over a four-meter distance. At 4000 – 4250 RPM, the team transmitted 15 bits per minute over a one-meter distance.