A hack-for-hire group tracked as Dark Basin targeted thousands of journalists, advocacy groups, and politicians worldwide over 7 years.
Researchers from Citizen Lab uncovered the operations of a hack-for-hire group tracked as Dark Basin that targeted thousands of journalists, elected and senior government officials, advocacy groups, and hedge funds worldwide over 7 years.
Dark Basin is a group of cyber mercenaries that conducted commercial espionage for its customers, the researchers from Citizen Lab linked it to BellTroX InfoTech Services (“BellTroX”), an Indian technology company.
“We give the name Dark Basin to a hack-for-hire organization that has targeted thousands of individuals and organizations on six continents, including senior politicians, government prosecutors, CEOs, journalists, and human rights defenders.” reads the report published by Citizen Lab.
“Over the course of our multi-year investigation, we found that Dark Basin likely conducted commercial espionage on behalf of their clients against opponents involved in high profile public events, criminal cases, financial transactions, news stories, and advocacy.”
The report published by the experts provides detailed info on several clusters of targets hit by the group.
According to researchers at Citizen Lab, more than 10,000 victim email accounts were targeted.
“A little-known Indian IT firm offered its hacking services to help clients spy on more than 10,000 email accounts over a period of seven years.” reported the Reuters agency.
Citizen Lab shared information about the attacks with the U.S. Department of Justice (DoJ) and is notifying additional targets of the hack-for-hire group.
Citizen Lab first uncovered the activity of the group in 2017 while investigating phishing attacks against a journalist. Attackers used a phishing link associated with a custom URL shortener, which was tied to a larger network of almost 28,000 URL shorteners containing the email addresses of targets.
The phishing messages were highly targeted, the group sent them to the targets from a range of email accounts, including Gmail accounts and self-hosted accounts. The Dark Basin group set up phishing sites that clones legitimate services like Google GMail, Yahoo Mail, and Facebook.
“While we initially thought that Dark Basin might be state-sponsored, the range of targets soon made it clear that Dark Basin was likely a hack-for-hire operation. Dark Basin’s targets were often on only one side of a contested legal proceeding, advocacy issue, or business deal.” continues the report.
“Sophistication of the bait content, specificity to the target, message volume and persistence across time varied widely between clusters. It appears that Dark Basin’s customers may receive varying qualities of service and personal attention, possibly based on payment, or relationships with specific intermediaries.”
Further investigation revealed that the Dark Basingroup was behind many other attacks over the past years, including the ones that hit at least two American advocacy groups who were requesting that the Federal Communications Commission (FCC) preserve net-neutrality rules in the U.S., U.S. non-governmental organizations Fight for the Future and Free Press, and journalists from multiple major U.S. media outlets.
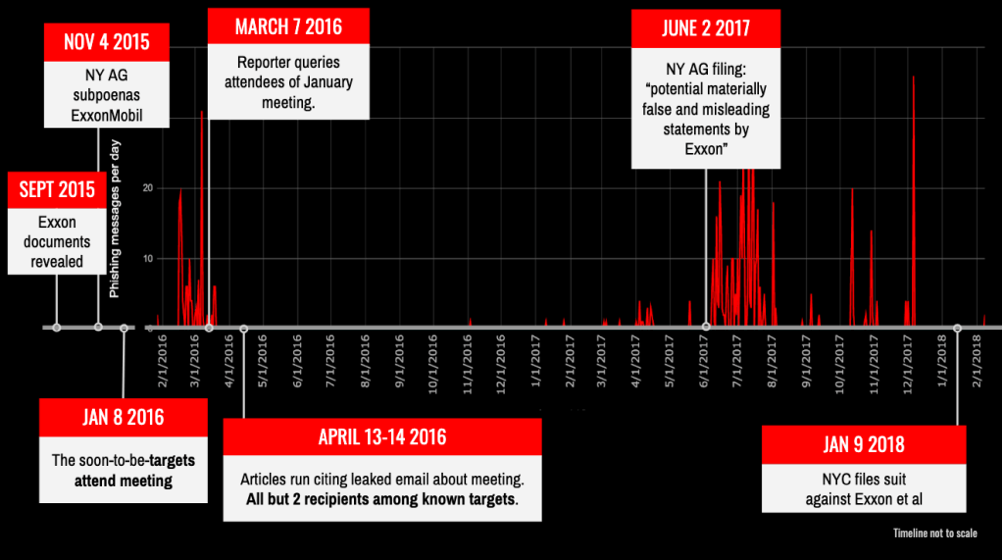
Among the American nonprofits targeted by the hackers there are some working on a campaign called #ExxonKnew aimed at demonstrate that ExxonMobil hid information about climate change for decades.
The operations of the group were surgical and threat actors always had a deep knowledge of the targets and of the events in which they were involved.
In 2016, theWall Street Journal received from an unknown source a private #ExxonMobil email inviting campaigners to a January 2016 meeting.
“The leak of the January 2016 email, as well as suspicious emails noticed by campaigners, led some present at the meeting to suspect their private communications may have been compromised,” said researchers. “We later determined that all but two recipients of the leaked January email were also Dark Basin targets.”
Researchers associated Dark Basin to the India-based technology company BellTroX InfoTech Services.
Among the clues gathered the researchers there are timestamps in the phishing emails were consistent with the working hours in India’s UTC+5:30 time zone and most of shortening services used by the group had names associated with India (i.e. Holi, Rongali and Pochanchi).
Experts also noticed that Dark Basin used BellTroX employees’ personal documents, including a CV, as bait while testing their URL shorteners.
The employees also shared on social media screenshots of links to Dark Basin infrastructure.
“We were able to identify several BellTroX employees whose activities overlapped with Dark Basin because they used personal documents, including a CV, as bait content when testing their URL shorteners. They also made social media posts describing and taking credit for attack techniques containing screenshots of links to Dark Basin infrastructure.” continues the post,
“BellTroX and its employees appear to use euphemisms for promoting their services online, including ‘Ethical Hacking’ and ‘Certified Ethical Hacker,’” they said. “BellTroX’s slogan is: ‘you desire, we do!’”
The employees were active since June 7, 2020, then the BellTroX’s website began displaying an error message, and materials linking BellTroX to the Dark Basin’ operations have been recently deleted.
“Dark Basin’s activities make it clear that there is a large and likely growing hack-for-hire industry. Hack-for-hire groups enable companies to outsource activities like those described in this report, which muddies the waters and can hamper legal investigations.” concludes the report.”Previous court cases indicate that similar operations to BellTroX have contracted through a murky set of contractual, payment, and information sharing layers that may include law firms and private investigators and which allow clients a degree of deniability and distance.”
Recently Google TAG has published its first TAG quarterly report, the Q1 2020 TAG Bulletin, that provides insights on the campaigns monitored in the first quarter of 2020.
The report includes recent findings on government-backed phishing, threats, and disinformation campaigns, as well as information about actions the tech giant has taken against accounts coordinated influence campaigns.
One of the most scaring trend reported by Google is the rising of hack-for-fire companies currently operating out of India.