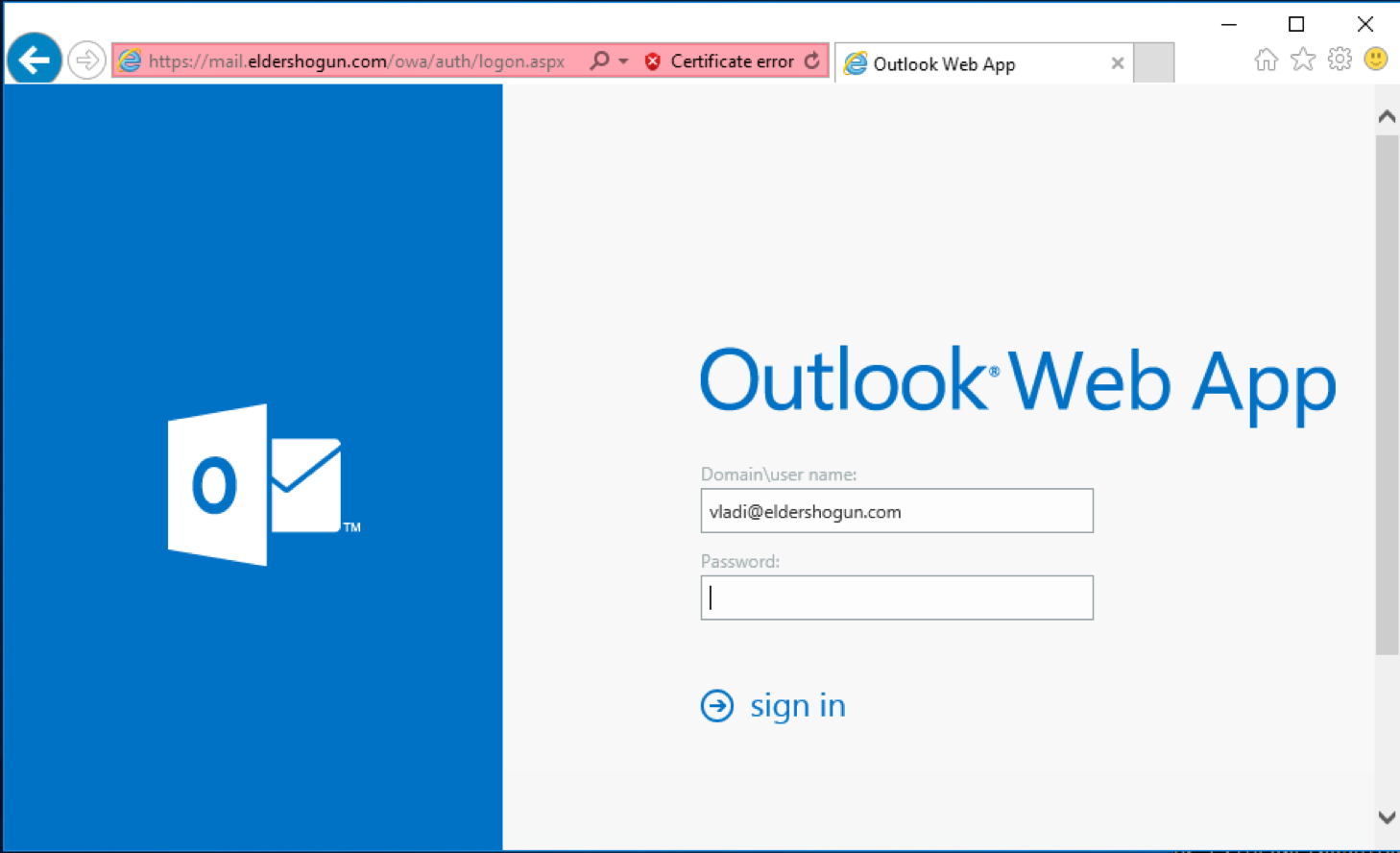
Enterprises running Exchange Server using two-factor authentication on Outlook Web Access (OWA) could be hacked due to a design flaw.
New troubles for enterprises running Exchange Server, two-factor authentication implementations on Outlook Web Access (OWA) could be easily bypassed due to a design flaw.
An attacker can bypass two-factor authentication to access email inboxes, calendars, contacts and other sensitive data of targeted enterprises.
The weakness is related to the fact that Exchange Server also exposes the Exchange Web Services (EWS) interface alongside OWA, but this is not protected by two-factor authentication.
The attackers can then hack OWA server by targeting EWS that shares the same port as Outlook Web Access.

The design issue disclosed last week by researcher Beau Bullock from Black Hills Information Security who privately reported it to Microsoft on Sept. 28.
Bullock explained that the principal problem is that Outlook Web Access and Exchange Web Services run on the same web server and are both enabled by default, and often enterprises ignore it.
Even enabling 2FA on OWA, EWS is still exposing a single factor authentication for the same infrastructure.
In his test, Bullock set up an OWA server protected by Duo for Outlook 2FA, then he targeted the EWS on the same server using a test account’s credentials.
Bullock used a tool called MailSniper that he developed for searching mailboxes for sensitive data in a Microsoft Exchange environment.
“At DerbyCon 6.0 I released a tool called MailSniper for searching mailboxes for sensitive data in a Microsoft Exchange environment. MailSniper utilizes Exchange Web Services (EWS) when connecting to an Exchange server to retrieve messages from a user’s inbox. EWS is a web-based API enabled on Exchange servers that Microsoft recommends customers use when developing client applications that need to interface with Exchange. ” Bullock wrote a blog post.
Below a video PoC published by the expert:
Summarizing, Bullock demonstrated that the lack of 2FA for Exchange Web Services could be exploited by attackers to hack into Outlook Web Access server.
“In conclusion, it appears that Outlook portals that are being protected by two-factor authentication might not be covering all of the authentication protocols to Microsoft Exchange. In this post it was demonstrated that Exchange Web Services is not being protected by a popular two-factor authentication software, and it was possible to still read emails of a user after only obtaining their login credentials. Exchange has other services that might have a similar problem such as MAPI over HTTP, and Autodiscover. I tested against one third-party 2FA software, and Microsoft’s own Azure Multi-Factor authentication but I’d imagine others likely have the same problem.” concluded Bullock.
[adrotate banner=”22″]