From August 2015 to February 2016 Buhtrap group managed to conduct 13 successful attacks against Russian banks for a total amount of $25.7 mln.
Since August of 2015, the Buhtrap group has conducted 13 successful attacks against financial institutions stealing more than ₽1.86 billion RUB ($27.4M USD). In April 2015, ESET discovered a malware campaign dubbed Operation Buhtrap, a conjunction of the Russian word for accountant “Buhgalter” and the English word “trap”. So far Buhtrap has not been seen anywhere else in the wild, 88 percent of targets have been in Russia and ten percent in Ukraine. Analysts have also likened the campaign to the Anunak/Carbanak campaign, which also targeted Russian and Ukrainian Banks.
The modus operandi of these particular cybercriminals is usually associated with targeted attacks rather than cyber fraud, which make this move to financial crime unusual and effective.
In the last wave of attacks, the hackers hit Russian banks by pretending to be FinCERT, a center established by the Russian Central Bank for dealing with cyber-attacks in Russia’s financial sector.
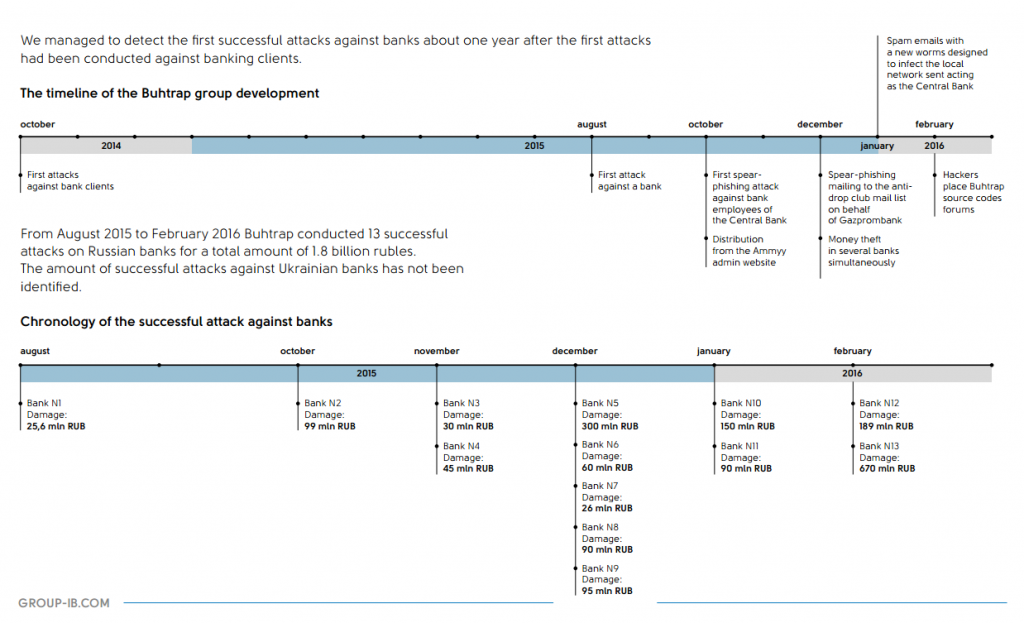
According to a report released by the security firm Group-IB, Buhtrap has been active since 2014, despite their first attacks against financial institutions were only detected in August 2015. Earlier, the group had only focused on targeting banking clients. At the moment, the group is known to target Russian and Ukrainian banks, below the timeline of the attacks published by Group-IB:

The Buhtrap timeline is a sequence of successful attacks, in August 2015 the hackers stole ₽25.6 million RUB ($375,617 USD), two months later a new campaign resulted in the losses of ₽99 million RUB ($1.4 million USD).
In November 2015, the group raked ₽75 million RUB ($1.1 million USD) with two distinct campaigns against two banks. In December the group reached a peak in its activity targeting 5 banks and taking down ₽571 million RUB ($8.3 million USD). They also conducted two successful attacks in January and two more a month later. In all, the group has stolen ₽1.86 billion RUB ($27.4M USD) from banks in Russia
The activities continued in January and February stealing dozen million dollars from banks in Russia.
In February 2016, a developer for Buhtrap leaked the complete source code for the malware used by the group because he wasn’t paid by the gang. Experts who have analyzed it discovered that the code is related to an earlier revision and not to the one used in the recent attacks.
“Earlier, the group had only focused on targeting banking clients. At the moment, the group is known to target Russian and Ukrainian banks.” states the report.
“In many respects, this group’s activity has led to the current situation where attacks against Russian banks causing direct losses in the hundreds of millions of rubles are no longer taken as something unusual,”
The tactic used by the Buhtrap group is consolidated, the hackers register typo domains or domains that are familiar to the victim, and from there they rent servers where mail servers were set up to send phishing emails on behalf of the legitimate company avoiding being filtered as spam.
The group used a custom malware which is able to detect security software and other defensive solutions. The malware uses to track every banking operation made by the victims, the malicious code notice these operations, it downloads a legitimate remote access tool (LiteManager) which is used to carry on fraudulent transfer orders.
What to expect in the next months?
The experts have no doubt, the group will continue its activity, likely improving its TTPs, researchers at Group-IB fears that the public availability of the gang’s malware may trigger the number of campaigns against banks conducted by other criminal organizations.
“The published source codes are active. Their wide distribution may trigger the increase in the number of attacks using this malware conducted by other groups. The builder interface is presented below.” states the report.
Let me suggest to give a look at the interesting report published by Group-IB, it is full of precious information on the Buhtrap group, including indicators of compromise.