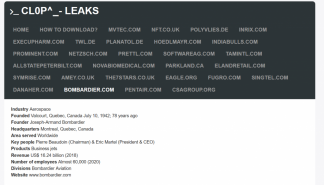
Hackers posted data stolen from manufacturer of business jets Bombardier on Clop ransomware leak site following alleged FTA hack.
Hackers exploited vulnerabilities in Accellion FTA file-sharing legacy servers to steal data from the airplane maker Bombardier and leak data on the site operated by the Clop ransomware gang.
The wave of attacks exploiting multiple zero-day vulnerabilities in the Accellion File Transfer Appliance (FTA) software began in mid-December 2020, threat actors use to deploy a shell dubbed DEWMODE on the target networks. Security experts from FireEye linked the cyber attacks to the cybercrime group UNC2546, aka FIN11. The attackers exfiltrate sensitive data from the target systems and then published it on the CLOP ransomware gang’s leak site.
It has been estimated that the group has targeted approximately 100 companies across the world between December and January.
Bombardier disclosed a security breach after some of its data was published on a dark web portal operated by the Clop ransomware gang.
“Bombardier announced today that it recently suffered a limited cybersecurity breach.” reads a statement published by the company. “An initial investigation revealed that an unauthorized party accessed and extracted data by exploiting a vulnerability affecting a third-party file-transfer application, which was running on purpose-built servers isolated from the main Bombardier IT network.”
The company notified appropriate authorities and hired cybersecurity and forensic professionals to investigate the incident.
The experts determined that personal and other confidential information relating to employees, customers and suppliers was compromised. The investigation indicates that the attackers had access only to data stored on the specific servers.
“Approximately 130 employees located in Costa Rica were impacted. Bombardier has been proactively contacting customers and other external stakeholders whose data was potentially compromised. The ongoing investigation indicates that the unauthorized access was limited solely to data stored on the specific servers.” continues the statement.
Bombardier pointed out that manufacturing and customer support operations have not been impacted.
The press release did not mention Accellion FTA servers, but confirmed that the company was hit as part of a campaign that targeted multiple organizations exploiting a vulnerability in an unnamed application.
Another circumstance that suggests the exploitation of the flaws in FTA servers was that the company systems were not encrypted with the Clop ransomware. The attack scenario is the one recently described by FireEye that linked the attack to the cybercrime gang FIN11.
Below a press release published by Accellion this week.
“Accellion does not access the information that its customers transmit via FTA. Following the attack, however, Accellion has worked at many customers’ request to review their FTA logs to help understand whether and to what extent the customer might have been affected. As a result, Accellion has identified two distinct groups of affected FTA customers based on initial forensics. Out of approximately 300 total FTA clients, fewer than 100 were victims of the attack. Within this group, fewer than 25 appear to have suffered significant data theft. Within this group, fewer than 25 appear to have suffered significant data theft.” reads the press release published by Accellion.
“These exploits apply exclusively to Accellion FTA clients: neither kiteworks nor Accellion the company were subject to these attacks.”
If you want to receive the weekly Security Affairs Newsletter for free subscribe here.
 Pierluigi Paganini
Pierluigi Paganini
International Editor-in-Chief
Cyber Defense Magazine


