A new Linux botnet uses Tor through a network of proxies using the Socks5 protocol, abuses legitimate DevOps tools, and other emerging techniques.
Researchers from Trend Micro have spotted a new Linux botnet employing multiple emerging techniques among cyber-criminals, including the use of Tor proxies, the abuse of legitimate DevOps tools, and the removal or deactivation of competing malware.
Experts highlighted that this Linux botnet downloads all the files it needs from the Tor network, including legitimate binaries like ss, ps, and curl. Botmasters maintain a big network of proxies that receive the connection coming from the surface web.
The malware also performs HTTP requests using shell script and Unix system design to get more information on the infected systems.
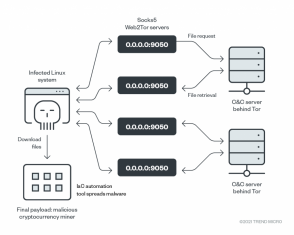
The malware leverages a network of proxies to convert the requests to the Tor network before reaching out to the server and retrieving the files. The proxies are used to send identifiable information about the infected system, including:
- IP addresses (randomized external and hashed internal)
- The operating system architecture
- The username currently running the script
- A part of the uniform resource identifier (URI) identifying the file to be downloaded (which is architecture-dependent)
- The file to be saved, where -o indicates the file name that should be saved (also randomized)
- The host name running the script
“We also discovered that most of the proxy servers used have open services with multiple vulnerabilities. These might be indicative of previous exploitation and deployment of the Tor proxy service without the knowledge of the server owner.” reads the analysis published by Trend Micro. “That the proxy service was always disabled after a while in our weeks-long monitoring of the proxies suggests that this is the case.”
The malware analyzed by the experts could run on different architectures using Linux-based OS, a circumstance that suggests that the botnet was involved in a wider campaign targeting Linux systems.
This is the first bot that abuses the infrastructure-as-code (IaC) tools, such as Ansible, Chef, and Salt Stack. for spreading.
The botnet is currently involved in cryptocurrency mining activity, it delivers the XMRig Monero (XMR) miner onto the infected machines. The binary includes a configuration file and unlike other cryptocurrency miners, it uses its own mining pool instead of public pools to make tracking attackers even more difficult.
“This malware sample does not need other software; the Linux operating system is the only requirement for the malware to run and spread. It downloads the essential tools (ss, ps, curl) because not every environment targeted for infection has them and it’s likely that the user doesn’t have the necessary permissions to install them on the system (as in the case of containers),” Trend Micro concludes. “Their weaponization of IaC tools suggests that these malicious actors are also well aware of the adoption of new technologies nowadays.”
If you want to receive the weekly Security Affairs Newsletter for free subscribe here.
Follow me on Twitter: @securityaffairs and Facebook
 Pierluigi Paganini
Pierluigi Paganini
International Editor-in-Chief
Cyber Defense Magazine


