Researchers from Kaspersky have spotted a new malware used by the WildPressure APT group to targets both Windows and macOS systems.
The WildPressure was spotted for the first time in August 2019 when researchers detected a never-before-seen malware, dubbed Milum, that had no similarities with other samples analyzed by the experts.
The Trojan was written in C++ and was employed attacks aimed at organizations from the Middle East. At least some of them are related to industrial sector.
Further investigation led to the discovery of other samples of the same malware that infected systems back in May, 2019.
Milum was compiled two months before, in March 2019, threat actors employed rented OVH and Netzbetrieb virtual private servers (VPS) and used domain registered with the Domains by Proxy anonymization service.
The analysis of the Milum code revealed that it doesn’t have similarities to malware involved in other operations attributed to known APT groups.
In September 2019, Kaspersky researchers were able to sinkhole one of the C2 domains used by the APT group (upiserversys1212[.]com). The vast majority of visitor IPs were also from the Middle East, specifically from Iran, while the rest were network scanners, TOR exit nodes or VPN connections.
Now the activity of the group resurfaced and threat actors upgraded the malware in their arsenal to expand operations and targets both Windows and macOS devices.
Kaspersky experts reported that the targets of the recent attacks are organizations in the oil and gas industry.
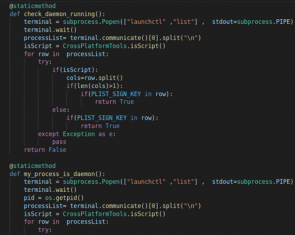
Experts discovered that the WildPressure also used Python as a programming language for its malware. The researchers discovered a PyInstaller module for Windows that contains a script named “Guard,” they also discovered that the malware was developed for both Windows and macOS OSs.
“The versioning system shows that the malware used by WildPressure is still under active development. Besides commercial VPS, this time the operators used compromised legitimate WordPress websites. With low confidence this time, we believe their targets to be in the oil and gas industry. If previously the operators used readable “clientids” like “HatLandid3”, the new ones we observed in the Milum samples appear to be randomized like “5CU5EQLOSI” and “C29QoCli33jjxtb”.” states the report published by Kaspersky.
The new Python-based Trojan extensively uses publicly available third-party code, once executed, it gathers system info (i.e. machine’s hostname, machine architecture, and OS release name) and sends themback to a remote server. The malicious code also enumerates running processes to check for installed anti-malware products, then awaits commands from the C2 server.
The Trojan supports multiple commands, including the ability to download and upload arbitrary files, execute commands, update the Trojan, and clean up, remove persistence and the script file from the infected host.
Kaspersky tracked the VBScript version of the malware as Tandis after its “serial” configuration parameter
The experts also found a number of previously unknown C++-based plugins that have been used to gather data on compromised systems.
Experts noticed that the threat actors used both VPS and compromised servers as part of their infrastructure, most of the compromised websites were running WordPress websites. The legitimate, compromised websites served as Guard relay servers.
Kaspersky found minor similarities between the WildPressure APT’s techniques and the ones used by another threat actor called BlackShadow, which also targets organizations in the Middle East.
“We consider with high confidence that the aforementioned Tandis VBScript, PyInstaller and C++ samples belong to the same authors that we dubbed WildPressure due to the very similar coding style and victim profile. However, another question remains: is WildPressure connected to other threat actors operating in the same region?” concludes the report. “Although we couldn’t associate WildPressure’s activity with other threat actors, we did find minor similarities in the TTPs used by BlackShadow, which is also active in the same region. However, we consider that these similarities serve as minor ties and are not enough to make any attribution.”
 Pierluigi Paganini
Pierluigi Paganini
International Editor-in-Chief
Cyber Defense Magazine

