Experts discovered 4,000 compromised installations on Amazon AWS of open source analytics and search tool Elasticsearch that were running PoS malware.
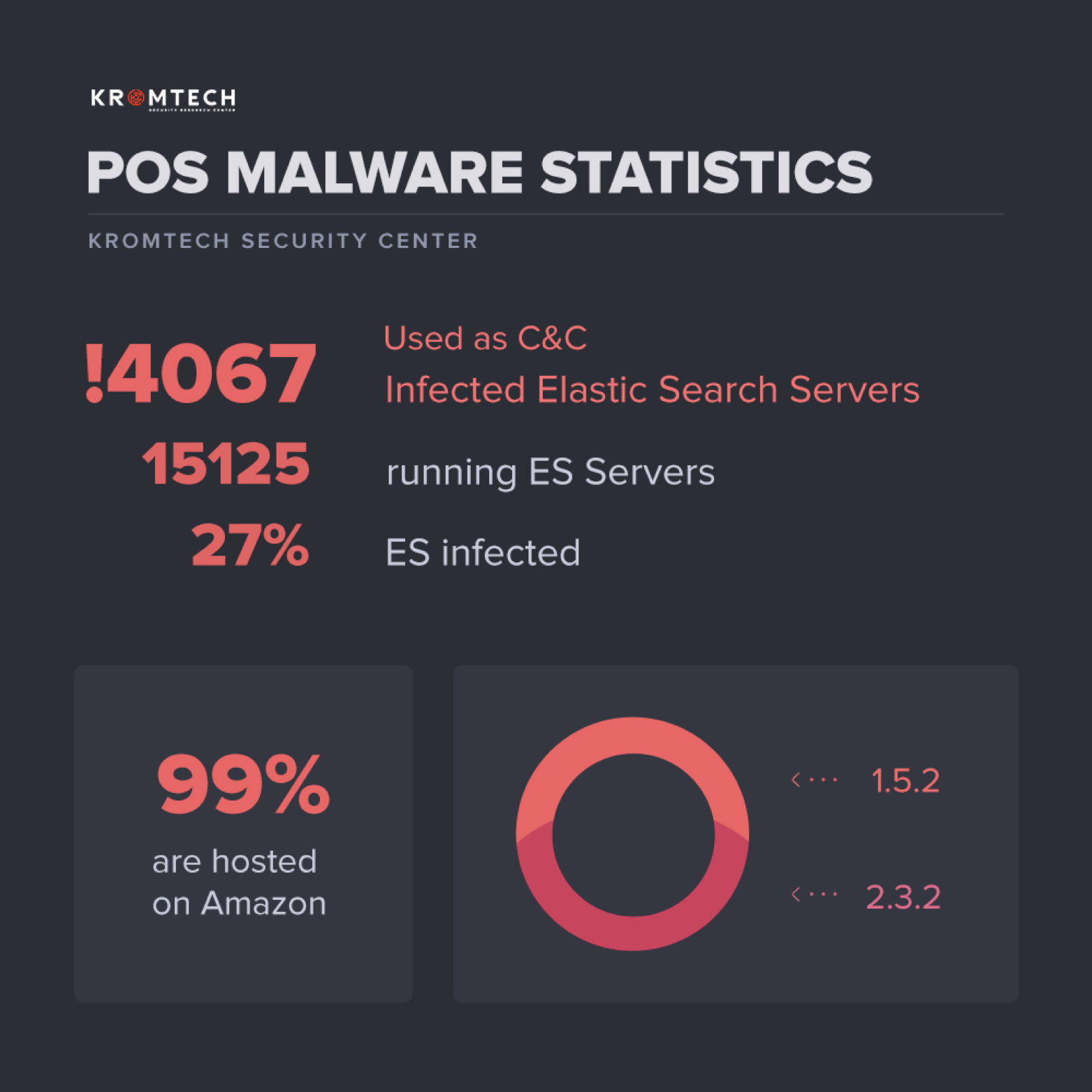
Security researchers from the firm Kromtech have discovered 4,000 compromised instances of open source analytics and search tool Elasticsearch that were running PoS malware.
According to Kromtech, this is just a portion of the overall number of compromised servers. Expert Bob Diachenko from Kromtech reported those servers are just 27 per cent of a total of 15,000 unsecured Elasticsearch installations discovered by the firm, and 99 per cent of the infected servers are hosted on Amazon AWS.
Amazon Web Services provides customers with a free T2 micro (EC2 / Elastic Compute Cloud) instance with up to 10 Gb of disk space, but clearly, customers are not able to properly secure the installs.
AWS offer only includes Elasticsearch versions 1.5.2 or 2.3.2, and unfortunately, users skip all security configuration during the quick installation process. Due to the poor settings are chosen by the operators, the malware is running with full administrative privilege on the compromised systems
“The Amazon hosting platform gives users the possibility to configure the ElasticSearch cluster just in few clicks, but usually, people skip all security configuration during the quick installation process. This is where a simple mistake can have big repercussions and in this case it did by exposing a massive amount of sensitive data.” wrote Diachenko.
The company found command-and-control servers for Alina and JackPoS point-of-sale malware running on the compromised Elasticsearch installs.
Threat actors are managing a big POS Botnet with Command and Control (C&C) that collects credit card information stolen from payment systems.
“The lack of authentication allowed the installation of malware on the ElasticSearch servers. The public configuration allows the possibility of cyber criminals to manage the whole system with full administrative privileges. Once the malware is in place criminals could remotely access the server’s resources and even launch a code execution to steal or completely destroy any saved data the server contains.” continues Diachenko.
Below the key findings of the research conducted by Kromtech:
- There are different packages of C&C malware, i.e. servers were infected multiple times
- Different packages can be related to different Botnets (because POS malware was seen selling not only on Darknet but on public domains as well)
- There is a lot of servers infected, for the same packages on different servers the time of infection could be different due to periodical scans and Botnets network expansion
- Nearly 99% of infected servers are hosted on Amazon Web Services
- 52% of infected servers run Elastic Search 1.5.2 version, 47% – 2.3.2 version, and 1% for other versions.
- Recent infections were made at the end of August 2017
Sysadmins must urgently check their Elasticsearch installs, analyze the connections and traffic, and check the presence of the PoS malware. In case of compromised installs, they can provide the sample to Kromtech before reinstalling the systems and apply patches as required.
[adorate banner=”9″]




 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.