The operators behind the MegalodonHTTP botnet have been arrested in an international joint effort of law enforcement and a private security firm.
In December, Norway law enforcement arrested five people accused of running the MegalodonHTTP Remote Access Trojan (RAT) as part of a joint operation between Norway’s Kripos National Criminal Investigation Service and Europol, codenamed “OP Falling sTAR.”
According to the Damballa security firm, the suspects were operating in Romania, France, and Norway and were charged with possessing, using and selling malware.
“Damballa’s threat discovery center worked in cooperation with the Norway police over the last few months to track and identify the author of the malware dubbed MegalodonHTTP,”threat researcher Loucif Kharouni wrote in a blog post.
“We are not at liberty to divulge the MegalodonHTTP author’s real identity, but we can confirm that the person behind the handle Bin4ry is no longer active or doing business.”
The men arrested by the law enforcement aged between 16 and 24 years, one of them already confessed to have operated a website which was offering for sale malware.
MegalodonHTTP is a Remote Access Trojan (RAT) that could be used by attackers to take over victims’ machines and exfiltrate sensitive data. According to the experts, the MegalodonHTTP is not a sophisticated threat, among the major flaws the need for the presence of the .Net framework on the infected machine.
“In contrast to it’s namesake, the malware is not very powerful; in fact it’s quite simple. It requires that .NET is installed on a device to run properly. Assuming that every recent machine with Windows has .NET installed and running by default, it shows the poor coding skills of the author – named Bin4ry. Usually malware authors don’t like to rely on dependencies – especially not .NET. This malware is sold on HackForum. Some criminals would refer to it as skid malware, or script kiddies, but its low price makes it attractive for others.” states a blog post published by Damballa on MegalodonHTTP RAT.
“Damballa’s threat discovery center worked in cooperation with the Norway police over the last few months to track and identify the author of the malware dubbed MegalodonHTTP,”threat researcher Loucif Kharouni wrote in a blog post.
“We are not at liberty to divulge the MegalodonHTTP author’s real identity, but we can confirm that the person behind the handle Bin4ry is no longer active or doing business.”
However, the researchers said MegalodonHTTP was not very powerful; in fact, it was “quite simple” and indicated the poor coding skills of its author, requiring .NET to be installed on infected systems.

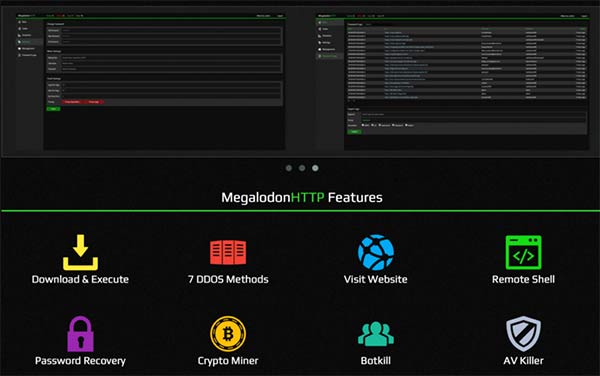
Below the list of features implemented MegalodonHTTP:
- Binary downloading and executing
- Distributed Denial of service (DDoS) attack methods
- Remote shell
- Antivirus Disabling
- Crypto miner for Bitcoin, Litecoin, Omnicoin and Dogecoin
The author was offering 2 different packages, at a cost of $35 and $100 respectively.
Package 1
- Web panel
- Stub
- Full support
Package 2
- Web panel
- Stub builder
- Full support
This operation is another success of the of the law enforcement, recently the Europol with Romanian police arrested eight criminal hackers suspected of being part of an international criminal ring that has stolen cash from ATMs using Tyupkin through Jackpotting attacks.