By Jobert Abma and Michiel Prins, Co-Founders at HackerOne
Reaching $100 Million in lifetime bounties paid ($100 Million!) reminded us of how much we appreciate everyone who has decided to join us on this journey — hackers, coworkers, customers, investors, and partners.
It means everything to us that our promise of transparency has helped transform the lives of countless hackers and that, together, we are promoting a culture of knowledge-sharing and community.
As a community, we are breaking the mold of traditional, secrecy-based security. Every day, hackers make organizations from the biggest corporations, to the fastest start-ups, to the most sensitive government and defense institutions demonstrably safer. And lawmakers and risk assessors from Washington, DC to Brussels to Singapore are taking notice. They acknowledge what we’ve known to be true all along. That safe harbor, vulnerability disclosure policies, and welcoming outside perspectives are hallmarks of a modern security posture. And hackers play the starring role.
We are really fired up and grateful about reaching $100 million in bounties because of what it says about how far hacker-powered security has come in a few short years.
This milestone also gives us a chance to reflect on the journey we’ve been on since founding HackerOne in 2012. We thought it would be fun to highlight just a few of the things that have surprised and inspired us along the way to this milestone.
We started out as a couple of hackers in the Netherlands with a crazy belief that people like us could make organizations safer and do it more efficiently and cost-effectively than traditional approaches. $100 Million in bounties later, maybe this idea isn’t so crazy after all.
We’ve since moved to San Francisco, grown to nearly 300 HackerOnies, over 700,000 hackers, and more than 1,900 customers. And we’ve never stopped hacking. In fact, in 2017 we squirrelled away all our bounty earnings to go on vacation. A vacation we finally took this February.
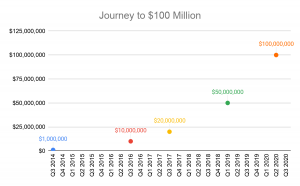
Throughout this journey, we’ve been consistently surprised and delighted by HackerOne’s accelerating rate of growth. Our first big bounties – $3,000 & $1,000 – came from Facebook. More important than supplying us with food and coffee money, this work introduced us to our co-founder’s arice. From this early $4,000 bounty, it took five years to get to $20 Million in bounties paid, a figure we reached in Q3 2017 (see chart). Since then, things have really taken off, with the next $80 Million taking only three years. We recently had our best week ever — $2.4 Million in bounties paid in just six days. With all the talk of the exponential growth of COVID-19 cases, we definitely prefer this chart!
Growing Pains Lead to Breakthroughs
HackerOne has been an international company from the start. And this meant paying hackers located all over the world. When we started, there were no good off-the-shelf solutions to this problem.
Sure, banks will let you do international transfers, but after all of the banks along the path to payment take their cut, the hacker receives an insulting fraction of the bounty they earned. So we ditched this approach and tried Western Union. This solved the middle man problem, but it was still a painfully manual. Western Union also limited the amount you could send in one transfer, so we would frequently need to divide bounties into multiple payments because high and critical bounties exceeded the maximum transfer amount. Turns out they were more useful than just sending money to the Nigerian prince that kept emailing about gold. But still, walking between Western Union branches was definitely not how we wanted to spend our time.
PayPal helped automate things somewhat, but even here we spent too much time importing and exporting CSV files. This is when we set out to create the HackerOne payment solution. We deliberately decided to write this as a separate system in its own codebase, but with tight interlock with the rest of the platform, because if it was *this* hard for us to pay people around the world, we figured others must be suffering as well. We thought we might spin it off as a separate product someday.
That never happened, but our global payment system did earn us some early customers. Specifically, Yahoo!, who at the time ran their own bounty program. They came to us initially just to manage the payout of bounty awards. Only later, after seeing all the other HackerOne platform features, did they move their entire program over to us.
The payment system also helped grow the hacker community. Once hackers were set up and had all the necessary tax documents on file (which was another hard lesson in working with bad APIs), it was a no-brainer for them to explore other programs.
With the benefit of hindsight, it’s not an overstatement to say that the HackerOne payment system served as a major catalyst for our growth.
From Bounties to Hacker-Powered Security
In the early days, bounties were our business. We connected security teams with hackers and earned a percentage when that introduction resulted in a valid vulnerability. If that sounds transactional, it’s because it was.
Over time, we observed something amazing and unexpected. Hackers were collaborating across time zones and cultures, sharing insights, tools, and techniques. What’s more, hackers and security teams running bounty programs were forming bonds that transcended a single report. More and more security teams realized hackers are an extension of their team. The kernel of a global online hacking community where each member invested in the growth and development of others began to take shape. Companies were starting to see the power of collaborating with individuals outside their walls. With this, the walls were coming down. The concept that secrecy and security go hand-in-hand was finally falling apart.
This was amazing to see and we asked ourselves, what can we do to nurture and grow this community? The extensive open source management experience of our CEO Mårten Mickos inspired our response, with launches of Hacker101, Hacktivity, live hacking events, and the bounty splitting feature, the latter in direct response to hackers wanting to share awards.
Working closely with our community and customers, we’ve been broadening the playing field and creating more opportunities for security teams and hackers to work together. Two obvious examples are Retesting and Pentesting. And we’re just getting started. Throughout the entire software development process, opportunities for hackers are abundant.
Retesting
As customers receive vulnerability reports and work on deploying fixes, they need to verify that vulnerabilities have actually been fixed properly. Many fixes are ineffective or incomplete, leaving uncontrolled residual risk. Having hackers retest is a great way for our customers to gain confidence in the fix and for hackers to add a new, steady source of income.
Pentesting
Pentests are a security staple used for compliance and as a periodic hygiene measure. HackerOne Pentest snaps right into an enterprises’ existing testing cadence and offers several advantages over traditional approaches, not least of which for times like these is remote-by-default. Rooted in teamwork, Pentest builds on the impressive multiplier effect we have seen work so well when hackers work in teams during Live Hacking Events. This is yet another way for hackers to monetize their existing skills and earn predictable income.
With both Retesting and Pentesting, HackerOne is growing the pie for hackers and helping customers shift hackers left and leverage the community’s diverse skills throughout the entire software development lifecycle.
We pin much of the success of this community and what we’ve been able to achieve together on HackerOne’s fundamental belief in the power of transparency to improve security and build trust. We see the power of this idea in the vibrancy of Hacktivity, the largest public repository of disclosed vulnerability reports, which lately has been growing by around 30 reports a week.
It’s important to point out that while we believe publicly disclosing closed and fixed vulnerability reports is a valuable and healthy security practice, whether, when, and how HackerOne clients disclose their program reports is completely up to them. Many do and many do not.
Publicly disclosing resolved bug reports is far from a fringe, Silicon Valley-only activity.
Those that do disclose reports on Hacktivity say that it helps them stay more secure since the closed reports are one of the best ways for new and existing hackers to learn. And smarter hackers make the internet safer for everyone. How so, you may wonder? More than once, a hacker has reviewed a disclosed report and found a new way to break it, sometimes by chaining it with other vulnerabilities. This kind of combinatorial, hive mind creativity is a hallmark of hacker-powered security. It’s why Together, We Hit Harder.
To close, making a new market is hard. But through the ingenuity of hackers, our great customers, and call us HackerOnies, together we are doing it. And we’re just getting started.
In tandem with the growth in bounties, we are seeing the term “hacker” used more and more in the way we use it: “One who enjoys the intellectual challenge of creatively overcoming limitations.” If you haven’t already, check out Hack for Good on our website where we celebrate hackers, and join us in showing the world #ThisIsWhatHackerLooksLike on Twitter.
Thanks again for being part of the journey with us to $100 million in bounties. We can’t wait to take the next leg of this trip with you.
#HackerOneHits100
About the Author
 Michiel Prins, Co-Founder and Product Lead
Michiel Prins, Co-Founder and Product Lead
- Michiel Prins is a co-founder and Product Lead at HackerOne, a technology company that connects organizations directly with hackers to find and resolve security issues. He is an information security expert, researcher, hacker, and developer. Michiel has been finding critical software vulnerabilities in technology for over 10 years. Prior to founding HackerOne, Michiel co-founded a successful penetration testing company that worked on projects for trusted organizations from government institutions to top technology companies, including Twitter, Facebook, Evernote, and Airbnb, among others. Michiel regularly presents on vulnerability disclosure and security research projects regarding security management, privacy, and web application infrastructure. Michiel graduated with a B.S. in Computer Science from Hanze University Groningen.
 Jobert Abma, Co-Founder and Technical Lead
Jobert Abma, Co-Founder and Technical Lead
- Jobert Abma is a co-founder and technical lead at HackerOne, the #1 bug bounty and vulnerability disclosure platform. He is an avid hacker, developer, and advocate for transparent and safe vulnerability disclosure. As a hacker himself, Jobert has reported critical vulnerabilities to GitLab, Yahoo, Slack, Snapchat among others. Before founding HackerOne, he was a successful penetration tester for a company he founded with customers included: Twitter, Facebook, Evernote, and Airbnb, among others. He studied Computer Science at Hanze University Groningen.
https://www.cyberdefensemagazine.com/wp-content/uploads/2020/05/Michiel-Prins-Author.jpg





 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.