By Carter Schoenberg, Vice President of Cybersecurity at SoundWay Consulting.
In the January issue of Cyber Defense Magazine, my first article provided an introduction to the Cybersecurity Maturity Model Certification (CMMC). My company has engaged with Government contractors since early January and I wanted to share some common issues that can be used as potential lessons learned as well as a lot has happened since this issue and I wanted to use this opportunity to go over these updates.
It is important to note that the industry continues to be at odds with the entire CMMC program. Regardless if those with dismay are cyber practitioners, former colleagues of the Accreditation Body, or even Organizations Seeking Certification (OSC), CMMC is moving forward per Ms. Katie Arrington of the Department of Defense and General Bassett who leads Defense Contract Management Agency (DCMA).
There was misguided speculation that President Joe Biden may suspend or overturn the CMMC program but no such luck for those seeking its demise. So now that we know CMMC is proceeding, what should Government Contractors (GovCons), do?
One critically important change to CMMC is the formal acknowledgment by Ms. Arrington that CMMC will have reciprocity for both FedRAMP and ISO 27001. This is very important because it conveys that an acceptance of other industry-accepted best practices galvanizes CMMC as genuine and authentic as well as provides options to OSCs to reduce their total costs of ownership in pursuing CMMC certification.
One hot topic continues to be what constitutes CUI, CTI. CDI, or even FCI. My suggestion is that as a GovCon you focus on the following:
- Identify what types of data sets you currently maintain, store, or transmit that are described in the NARA CUI Registry.
- Identify what types of contracts you currently are pursuing and identify what data sets may be applicable in the future.
As a reminder, unless you have a reasonable belief that CUI will be in play, the Department of Defense is advising GovCons to prepare for Maturity Level 1, which consists of 17 practices derived from NIST SP800-171. Two things to consider here. First, NIST SP 800-171 has a new version out (Revision 2). Second, even if you have a reasonable belief you do not (nor will you ever) have CUI, it doesn’t matter and here are the reasons why.
- The Government now has specific requirements that if a clause trigger is in your future contract for safeguarding, then you will have to upload a self-assessment into the Supplier Performance Risk System (SPRS).
- Large Prime Contractors are forcing their subs to complete the self-attestation, regardless.
First lesson learned – CMMC vs. Self-Assessment
On one hand you have a directive to meet 17 practices and in the same breath, you have to score yourself against 110 controls from NIST SP800-171. Our company is seeing numerous companies attempting to complete these self-assessments on their own with little or no understanding of the goals and objectives of each practice. This presents the probability of mis-scoring in a way that is inaccurate and favors the GovCon. DCMA has already advised these submissions are likely to be audited first if the score is unreasonably high.
Second lesson learned – Other Defined Costs (ODCs)
In a session held the last week of January, the topic of costs that can be reimbursed by the Department of Defense came up and I was all eyes and ears open because this has been a hot topic for me as well. Values of $3,000.00 to become CMMC L1 and so on were being socialized and that figure is not consistent with what is consistent with industry by a long shot. Then the clarification came. In this scenario of CMMC L1, the Government has determined that $3,000.00 is a reasonable independent cost estimation to “obtain” certification. It does not account for “preparation there to”.
As I am sure you can imagine, the preparation represents the lion share of the associated costs with conforming with CMMC requirements and subsequently, the interim DFARS rule. So what are GovCons to do about these costs? In two simple words, you will have to “absorb it”. There is a new Sheriff in town and it doesn’t care about what preparation costs you. Why? Most likely because GovCons have been attesting in the Reps and Certs with their proposals that they were already conforming to NIST SP 800-171 so why would the Government pick up a tab where a claim of compliance already exists?
Third lesson learned – Top Common Factors Not Addressed
The information described comes from a very small sample set but is consistent when compared against numerous engagements I have performed since 2015. There are a number of things necessary to meet CMMC requirements at Maturity Level 3 and higher that seem to go unaddressed by GovCons. This includes, but not limited to:
- A lack of separation of duties
- A lack of an existing system security plan
- A lack of specified training for cybersecurity and privacy (please note what is provided by the DOD) for information security is not consistent with the goals and objectives for the AT Family in NIST 800-171 and CMMC
- A lack of incident response planning capability (Policy, playbook, etc.) that has been operationalized into corporate culture
- A lack of legally binding agreements (Service Level Agreements, Teaming Agreements, Terms and Conditions, etc.) that clearly specify CMMC or even general cybersecurity best practices as mandatory to better define where the offeror’s liability starts and the offerree’s end.
Fourth lesson learned – Unrealistic Timetable to Implement and Kicking the Can
Bothe the Government and Accreditation Body have socialized a six-month runway that GovCons should leave to prepare for CMMC L3 certification. Because a large number of solicitations have yet to include, the vast majority of GovCons are kicking the can down the road taking an approach of “I will deal with it when I see it in writing”. While I understand the thought, by the time you see it in a solicitation it is too late. As stated in the January article, there is a delta of two months between preparation time and the lifecycle of an aware. You should allow between 8-12 months to be more realistic. In the following image taken from a CMMC-AB Town Hall session (image available for public release), we see an example of a four-month window from RFP to Award.
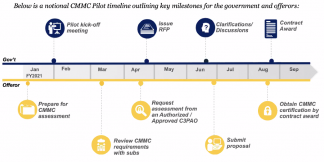
Figure 1. Provided by CMMC-AB Town Hall Session
Plan wisely, spend judiciously.
About the Author
 Carter Schoenberg is the Vice President of Cybersecurity at SoundWay Consulting. Carter has over 20 years’ experience supporting Government and Industry stakeholders and is a subject matter expert on the Cybersecurity Maturity Model Certification (CMMC), cyber investment strategies, reducing organizational exposure to harm by cyber liabilities. His work products have been used by DHS, DOD, NIST, and the ISAC communities.
Carter Schoenberg is the Vice President of Cybersecurity at SoundWay Consulting. Carter has over 20 years’ experience supporting Government and Industry stakeholders and is a subject matter expert on the Cybersecurity Maturity Model Certification (CMMC), cyber investment strategies, reducing organizational exposure to harm by cyber liabilities. His work products have been used by DHS, DOD, NIST, and the ISAC communities.
Carter can be reached online at [email protected] and through www.soundwayconsulting.com or the CMMC Marketplace





 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.