Operators behind the Necurs botnet, the world’s largest spam botnet, are currently using a new evasion technique attempting to surprise the unprepared defenses.
Necurs is the world’s largest spam botnet, it is composed of millions of infected computers worldwide.
Necurs was not active for a long period at the beginning of 2017 and resumed its activity in April 2017. The Necurs botnet was used in the past months to push some malware, including Locky, Jaff, GlobeImposter, Dridex , Scarab and the Trickbot.
In February security experts observed the Necurs botnet was used to send out an amazing number of messages offering companionship waiting for Valentine’s day.
According to the IBM X-Force team, the campaign started in mid-January, it leveraged the overall Necurs botnet that has been estimated as composed of 6 million bots.
Now the botnet made the headlines again, the author implemented a new evasion technique. Crooks are sending out an email to a potential victim containing an archive file that once unzipped will present a file with the extension of .URL.
The .URL extension is associated with Windows shortcut file that opens an URL into a browser, in the campaign observed by the experts it points to a remote script file that downloads and executes a final payload.
In this last campaign, Necurs is delivering the Quant Loader to the victims to download another malware.
“As security vendors are wise to Necurs’s traditional infection chain (a script, a macro, or archives containing certain file formats), the malware has started using an internet shortcut or .URL file to bypass detection.” reads the analysispublished by Trend Micro.
“Previously, Necurs’s JavaScript downloader downloads the final payload. But in its latest iteration, the remote script downloads QUANTLOADER (detected by Trend Micro as TROJ_QUANT) – a different downloader – which then downloads the final payload. This is another layer added to Necurs’s infection chain.”
The abuse of .URL files is a novelty for Necurs operators. according to the researchers, this technique implements a simplified infection chain compared to spam techniques used in the past.
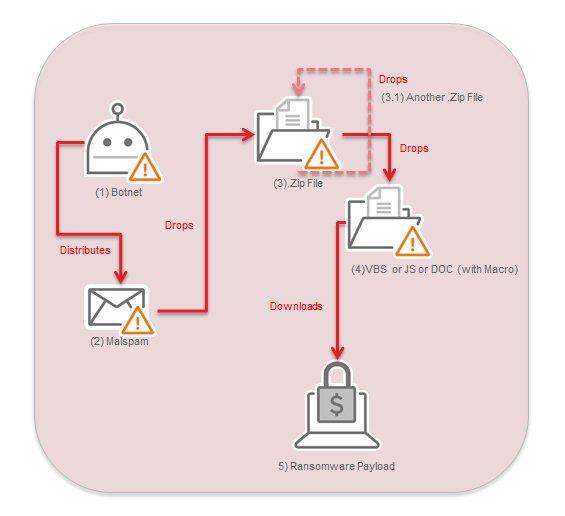
“Last year, we also saw how Necurs pushed double-zipped attachments that either contained JavaScript, Visual Basic scripts, or macro files with the capability to download itsfinal payload.” continues the analysis.
“In an attempt to evade spam detection through its attachments, Necurs used archives that included .ZIP files to disguise the script downloader, which was later enclosed in another .ZIP to hide itself.”
This simple infection chain allows avoiding anti-malware solutions that scan emails, looking for malicious links, boobytrapped attachments or other malicious patterns associated with an attack.
Of course, once uncovered the new campaign, the security firms will update existing detection rules to rapidly discovers attacks and neutralize the spam campaign.
Malware researchers added that crooks are using the standard folder icon to hide .URL files to deceive victims on their malicious nature.
Once the victim has clicked on the archive it extracts a file that appears to the victims as a new folder on their PC. When the victims click on the folder to explore its content they will start the infection chain.
“Notice that aside from the icons disguised as folders, the filenames were also crafted to resemble typical folder names such as IMG-20180404-9AC4DD, SCN-20180404-268CC1, and PIC-20180404-ADEEEE shown in Figure 2, to name a few.” states Trend Micro.
Now that you know this new technique … open the eyes and remain vigilant.




 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.