Russia-linked APT group Turla has been using a sophisticated backdoor, dubbed LightNeuron, to hijack Microsoft Exchange mail servers.
Russia-linked APT group Turla has been using a sophisticated backdoor, dubbed LightNeuron, to hijack Microsoft Exchange mail servers.
Turla group (also known as Waterbug, Venomous Bear and KRYPTON) has been active since at least 2007 targeting government organizations and private businesses.
The list of previously known victims is long and includes also the Swiss defense firm RUAG, US Department of State, and the US Central Command.
Attackers use the LightNeuron malware to access and modify any email passing through the compromised mail server. It also allows create new emails and prevents that messages reach the intended recipients.
Malware researchers believe Turla is using the malware at least since 2014 to target Microsoft Exchange servers. The experts only analyzed a Windows version of the malicious code, but evidence suggests the existence of a Linux version as well.
“This backdoor, dubbed LightNeuron, has been specifically targeting Microsoft Exchange mail servers since at least 2014. Although no samples were available for analysis, code artefacts in the Windows version lead us to believe that a Linux variant exists.” reads the analysis published by ESET.
ESET has identified at least three different organizations that have been infected with the malware, including a Ministry of Foreign Affairs in an Eastern European country, a regional diplomatic organization in the Middle East, and an unknown organization in Brazil.
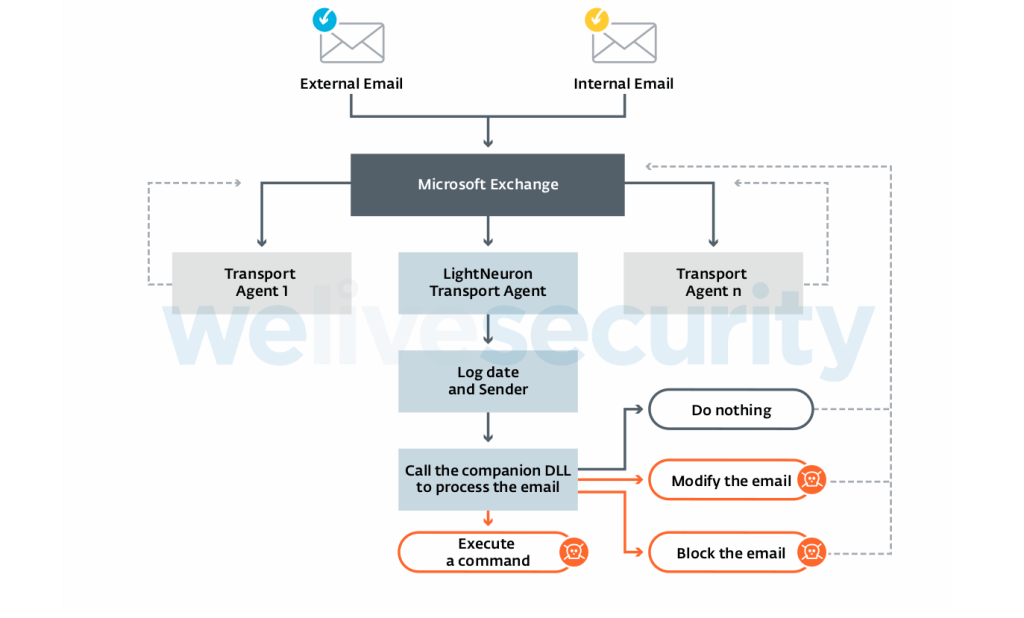
LightNeuron is the first malware specifically designed to target Microsoft Exchange email servers, it runs with the same level of trust as spam filters and other security products.
“LightNeuron is, to our knowledge, the first malware specifically targeting Microsoft Exchange email servers. It uses a persistence technique never before seen: a Transport Agent.” continues the analysis. “In the mail server architecture, it operates at the same level of trust as security products such as spam filters. Figure 3 summarizes how LightNeuron operates.”
LightNeuron supports many commands, including executing processes and commands, writing/executing/deleting files, exfiltrating files, and disabling the backdoor for x minutes.
Attackers control the malware using emails containing specially crafted PDF documents or JPG images as attachments. Commands are hidden in the attachments using steganography.
Researchers at ESET pointed out that compromised Exchange servers received commands mostly during work hours in UTC+3, the Moscow time zone. The activity of attackers was temporarily suspended between December 28, 2018, and January 14, 2019, that match the Christmas period for the Orthodox church.
“LightNeuron is a very powerful piece of malware. It can spy on all the emails of the compromised organization but also execute commands, for example, to control other machines on the local network. This makes it a main hub in the breached network for Turla operators.” concludes the report.
On August, ESET published a detailed report on another variant of the Turla backdoor that leverages email PDF attachments as command and control.
ESET shared a full list of Indicators of Compromise (IoCs) and samples in a white paper and on GitHub.




 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.