IBM’s security researchers demonstrated that the Siri Shortcuts introduced in the Apple iOS 12 can be abused by attackers.
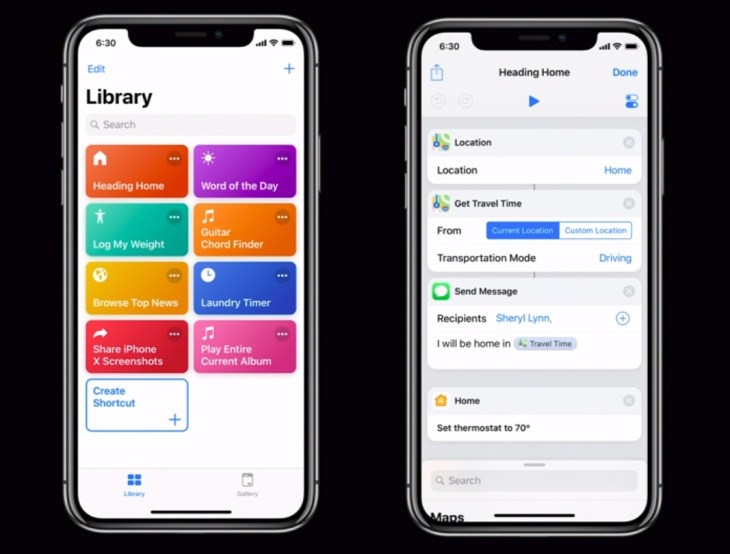
Apple implemented Siri Shortcuts in the iOS 12 to allow users to rapidly access to applications and features, they can automate common tasks and can be integrated by third-party developers in their software.
Researchers at IBM Managed Security Services discovered that
Siri Shortcuts can be abused by hackers to perform malicious activities.
“This new feature can be enabled via third-party developers in their apps, or custom built by users downloading the shortcuts app from the app store. Once downloaded and installed, the Shortcuts app grants the power of scripting to perform complex tasks on users’ personal devices.” reads the analysis published by IBM.
“But accessing the phone from Siri Shortcuts also presents some potential security risks that were discovered by X-Force IRIS and reported to Apple’s security team.”
Experts pointed out that Siri Shortcuts improve interactions between users and the device, it allows the implementation of access directly from the lock screen or through existing apps. Users can also share the Shortcuts from the apps via iCloud.
The shortcuts can be presented by developers on the lock screen or in ‘search’ field, based on time, location and context.
“The shortcut can then appear on the lock screen or in ‘search’ when it is deemed appropriate to show it to the user based on time, location and context.” continues the analysis.
“For example, a user approaches their usual coffee shop, and the relevant app pops up a shortcut on the screen to allow them to order the usual cup of java and pay for it on the app before they even enter the coffee shop.”
Experts at IBM explained that the new feature could be used to create for malicious purposes such as scareware, a pseudo ransom campaign that attempts to scare victims and trick them into paying attackers by making them believe their data were stolen by hackers.
The attackers can use native shortcut functionality, they can develop a script to provide the ransom demands to the device’s owner by using Siri’s voice. Attackers can also automate data collection from the device (user’s current physical address, IP address, contents of the clipboard, stored pictures/videos, contact information and more) and send them to the victims to scare them.
“To move the user to the ransom payment stage, the shortcut could automatically access the Internet, browsing to a URL that contains payment information via cryptocurrency wallets, and demand that the user pay-up or see their data deleted, or exposed on the Internet,” continues the post.
What’s making this attack scenario more scaring is that the attacker could configure the malicious Shortcut to spread to the victim’s contact list, with this trick they prompt potential victims to download and install the malicious Shortcut.
Below a video PoC of the hack that shows how a Shortcut can change the device’s brightness and volume, can speak a ransom note that includes convincing personal details, can turn the flashlight on and off while vibrating at the same time, can display the spoken note in a written alert, and access the URL of a page containing payment information, in addition to spreading via messages to users’ contacts.
https://youtu.be/PlgPSwwZc80
“In our security research labs, we tested the ransom attack scenario. The shortcut we created was named ‘Ransom’ in the video, but it could easily be named any other name to entice users to run it. Lures, such as game cheats/hacking, unlocking secret functionality in apps, or getting free money, often entice users to tap on a shortcut and see where it leads,” explained John Kuhn, senior threat researcher at IBM Managed Security Services.
Siri Shortcuts open the door to a broad range of social engineering attacks, they could be abused to trick victims into installing any kind of malware on their devices.
Below some recommendations shared by the experts:
- Never install a Shortcut from an untrusted source.
- Check the permissions that the shortcut is requesting and never give permission to portions of your phone you are not comfortable with. Things like photos, location and camera could be used to obtain sensitive information.
- Use the show actions button before installing a third-party shortcut to see the underlying actions the shortcut might take. Look for things like messaging data to numbers you don’t recognize, emailing data out, or making SSH server connections to servers.




 We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.
We are in our 11th year, and Global InfoSec Awards are incredibly well received – helping build buzz, customer awareness, sales and marketing growth opportunities, investment opportunities and so much more.